Enterprise Managed Users の SAML SSO について
Enterprise Managed Users では、GitHub.com のエンタープライズ リソースへのアクセスは、ID プロバイダー (IdP) を介して認証する必要があります。 GitHub ユーザー名とパスワードを使用して GitHub にサインインする代わりに、エンタープライズのメンバーは IdP を介してサインインします。
SAML SSO を構成した後は、IdP が利用できない場合に Enterprise へのアクセスを回復できるように、回復用コードを格納することをお勧めします。
現在、認証に SAML SSO を使っており、OIDC を使って CAP サポートの恩恵を受けたい場合は、移行パスをたどることができます。 詳しくは、「SAML から OIDC への移行」を参照してください。
前提条件
-
IdP の統合要件とサポート レベルを理解していることを確認します。 詳しくは、「Enterprise Managed Users について」を参照してください。
-
IdP は SAML 2.0 仕様に準拠している必要があります。 詳細については、OASIS の Web サイトの SAML Wiki を参照してください。
-
Enterprise Managed Users で SAML SSO 用に IdP を構成するには、IdP に対するテナントと管理アクセス権が必要です。
Enterprise Managed Users の SAML SSO の構成
マネージド ユーザーを含む Enterprise の SAML SSO を構成するには、IdP でアプリケーションを構成してから、GitHub.com でエンタープライズを構成する必要があります。 SAML SSO を構成したら、ユーザー プロビジョニングを構成できます。
IdP を構成する
-
パートナー IdP を使用する場合、GitHub Enterprise Managed User アプリケーションをインストールするには、次のいずれかのリンクをクリックします。
-
Azure Marketplace の Microsoft Entra ID アプリケーション (Entra ID の旧称は Azure AD です)
-
Okta の統合ディレクトリ内の Okta アプリケーション
-
- PingFederate コネクタをダウンロードするには、 [アドオン] タブに移動して、 [GitHub EMU Connector 1.0] を選びます。
-
-
IdP で Enterprise Managed Users の SAML SSO を構成するには、次のドキュメントを参照してください。 パートナー IdP を使用しない場合は、GitHub Enterprise Cloud の SAML 構成リファレンスを使用して、IdP に汎用 SAML 2.0 アプリケーションを作成して構成できます。
- Microsoft Learn の Entra ID
- Okta ドキュメントの Okta の手順
- PingIdentity ドキュメントの PingFederate 命令
- 「SAML 構成リファレンス」
-
Enterprise をテストして構成するには、自分または GitHub.com でエンタープライズの SAML SSO を構成するユーザーを、IdP で Enterprise Managed Users 用に構成したアプリケーションに割り当てます。
-
GitHub.com で Enterprise を引き続き構成するには、IdP にインストールしたアプリケーションから次の情報を見つけてメモします。
値 その他の名前 説明 IdP のサインオン URL ログイン URL、IdP URL IdP 上のアプリケーションの URL IdP 識別子 URL 発行者 SAML 認証用のサービス プロバイダーに対する IdP 識別子 署名証明書 (Base64 エンコード) 公開証明書 IdP が認証要求に署名するために使用する公開証明書
エンタープライズを設定する
IdP で Enterprise Managed Users の SAML SSO を構成した後、GitHub.com でエンタープライズを構成できます。
SAML SSO の初期構成後、既存の SAML 構成の GitHub.com で更新できる設定は SAML 証明書のみです。 サインオン URL または発行元 URL を更新する必要がある場合は、まず SAML SSO を無効にしてから、新しい設定で SAML SSO を再構成する必要があります。 詳しくは、「Enterprise Manged User の認証とプロビジョニングを無効にする」を参照してください。
-
ユーザー名 @SHORT-CODE_admin を使って、Enterprise のセットアップ ユーザーとして GitHub.com にサインインします。SHORT-CODE は、Enterprise の短いコードに置き換えます。
注: セットアップ ユーザーのパスワードをリセットする必要がある場合、GitHub Support ポータル から GitHub Support に問い合わせます。
-
GitHub.com の右上の自分のプロファイル写真をクリックし、 [自分の Enterprise] をクリックします。
-
Enterpriseのリストで、表示したいEnterpriseをクリックしてください。
-
Enterprise アカウントのサイドバーで、 [設定] をクリックします。
-
[設定] で、 [認証セキュリティ] をクリックします。
-
[SAML シングル サインオン] で、 [Require SAML authentication](SAML 認証が必要) を選択します。
-
[サインオン URL] に、IdP の構成時にメモした SSO 要求の IdP の HTTPS エンドポイントを入力します。
-
[発行者] に、IdP の構成時にメモした SAML 発行者 URL を入力して、送信されたメッセージの信頼性を確認します。
-
[公開証明書] で、IdP の構成時にメモした証明書を貼り付けて、SAML 応答を確認します。
-
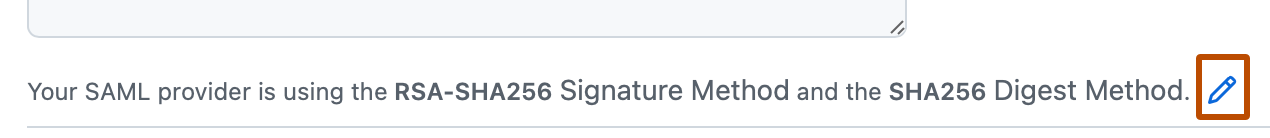
公開証明書で、現在のシグネチャ メソッドとダイジェスト メソッドの右側にある をクリックします。
-
[シグネチャ メソッド] と [ダイジェスト メソッド] のドロップダウン メニューを選び、SAML 発行者が使っているハッシュ アルゴリズムをクリックします。
-
エンタープライズで SAML SSO を有効化する前に、 [Test SAML configuration](SAML 構成のテスト) をクリックして、入力した情報が正しいか確認します。 このテストではサービス プロバイダーによって開始される (SP によって開始される) 認証が使われ、SAML 設定を保存するにはこれに成功する必要があります。
-
[保存] をクリックします。
注: Enterprise に SAML SSO を要求すると、セットアップ ユーザーは Enterprise にアクセスできなくなりますが、GitHub にはサインインしたままになります。 IdP によってプロビジョニングされた マネージド ユーザー アカウント のみがエンタープライズにアクセスできます。
-
将来的に ID プロバイダーが利用できなくなった場合でも エンタープライズ GitHub.com にアクセスできるように,[ダウンロード],[印刷],または [コピー] をクリックして回復コードを保存してください。 詳しくは、「エンタープライズ アカウントのシングル サインオンの回復コードをダウンロードする」を参照してください。
プロビジョニングの有効化
SAML SSO を有効にした後、プロビジョニングを有効にします。 詳しくは、「エンタープライズ マネージド ユーザーの SCIM プロビジョニングの構成」を参照してください。
ゲスト コラボレーターの有効化
ゲストコラボレータのロールを使用して、企業内のベンダーや請負業者に限定的なアクセス権を付与できます。 エンタープライズ メンバーとは異なり、ゲスト コラボレーターは、メンバーである組織内の内部リポジトリにのみアクセスできます。
SAML 認証に Entra ID または Okta を使用する場合は、ゲスト コラボレーターを使用するように IdP アプリケーションを更新することが必要な場合があります。 詳しくは、「ゲスト コラボレーターの有効化」を参照してください。