Сведения о частной сети Azure для GitHubразмещенных в runners
Вы можете использовать GitHubразмещенных в виртуальной сети Azure. Это позволяет использовать GitHubуправляемой инфраструктурой для CI/CD, обеспечивая полный контроль над сетевыми политиками запуска. Дополнительные сведения о виртуальной сети Azure см. в статье "Что такое Azure виртуальная сеть?" в документации По Azure.
Вы можете подключить несколько подсетей виртуальной сети к GitHub.com и управлять доступом к частному ресурсу для пользователей с помощью групп runner. Дополнительные сведения о группах runner см. в разделе "Управление доступом к крупным средствам выполнения".
Использование GitHubразмещенных в виртуальной сети Azure средств выполнения позволяет выполнять следующие действия.
- При частном подключении средства выполнения к ресурсам в виртуальной сети Azure без открытия интернет-портов, включая локальные ресурсы, доступные из виртуальной сети Azure.
- Ограничьте доступ или подключение пользователей с помощью GitHub, размещенных в среде runner, с полным контролем над политиками исходящей сети.
- Отслеживайте сетевые журналы для GitHubразмещенных в среде runner и просматривайте все подключения к средству выполнения и из нее.
Сведения об использовании более крупных модулей выполнения с виртуальной сетью Azure
С виртуальной сетью Azure поддерживаются 2-64 виртуальных ЦП Ubuntu и Windows. Дополнительные сведения об этих типах runner см. в разделе "О более крупных бегунах".
Частная сеть для GitHubразмещенных в среде runners не поддерживает статические IP-адреса для более крупных модулей выполнения. Необходимо использовать динамические IP-адреса, которые являются конфигурацией по умолчанию для более крупных модулей выполнения. Дополнительные сведения о сети для крупных runners см. в разделе "О более крупных бегунах".
Сведения о сетевом обмене данными
Чтобы упростить обмен данными между сетями GitHub и виртуальной сетью, развертывается сетевой интерфейс карта (сетевой адаптер) в виртуальной сети Azure с помощью .
Так как сетевой адаптер находится в виртуальной сети, GitHub не может блокировать входящие подключения. По умолчанию виртуальные машины Azure будут принимать входящие подключения из той же виртуальной сети. Дополнительные сведения см AllowVNetInBound . в Microsoft Learn. Рекомендуется явно блокировать все входящие подключения к средствам выполнения. GitHub никогда не требует входящих подключений к этим компьютерам.
Сетевой адаптер позволяет виртуальной машине Azure взаимодействовать с Интернетом, Azure и локальными ресурсами. Таким образом, все обмен данными остается закрытым в пределах сети, а политики сети, применяемые к виртуальной сети, также применяются к средству выполнения. Дополнительные сведения об управлении сетевым интерфейсом см. в разделе "Изменение параметров сетевого интерфейса" в Microsoft Learn.
Note
Несколько сетевых адаптеров могут отображаться для одного задания в подписке, так как служба GitHub Actions переопределила ресурсы для выполнения заданий. После простоя средство запуска GitHub Actions автоматически отменяет подготовку ресурса и удаляет соответствующий сетевой адаптер.
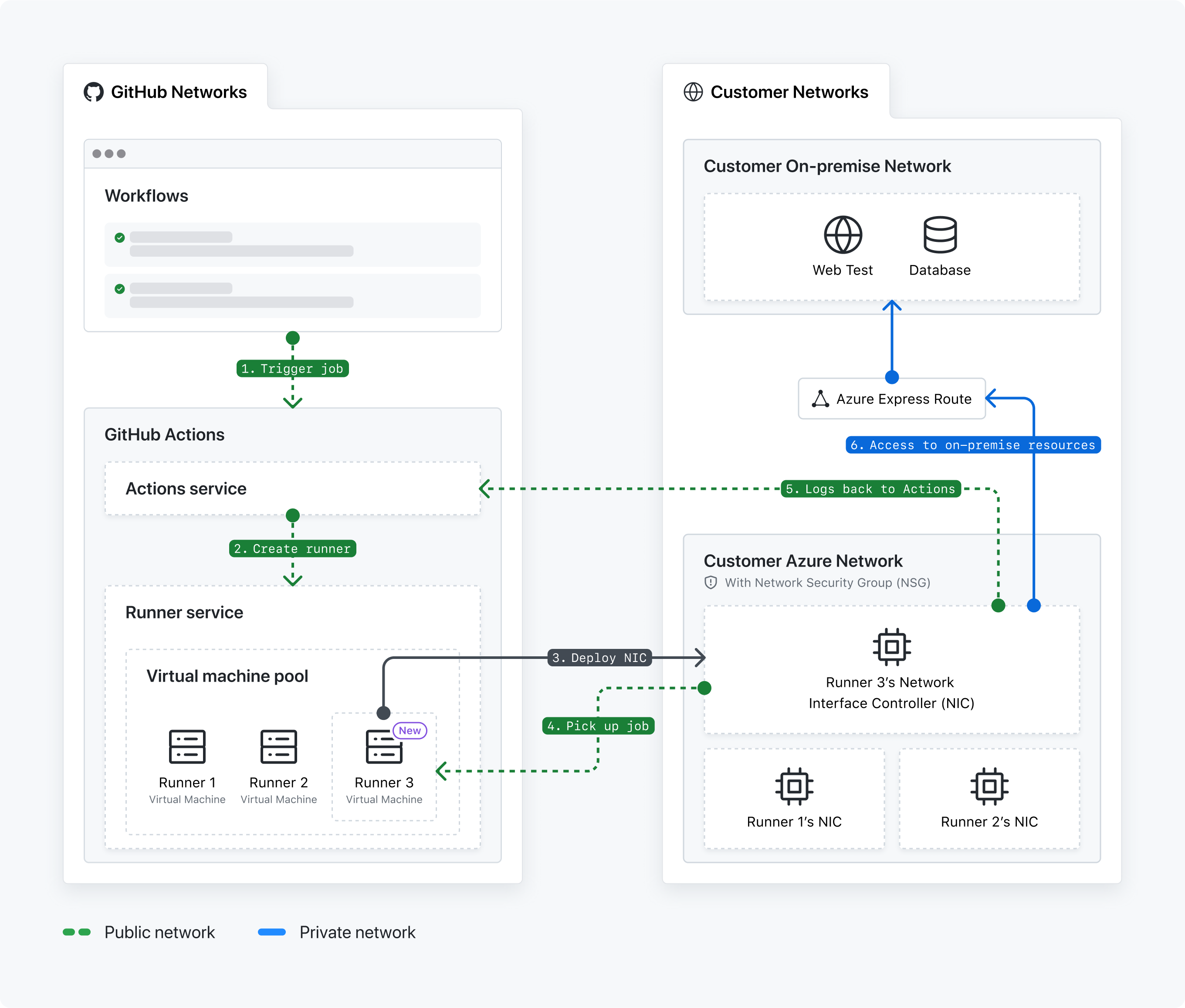
- Активируется рабочий процесс GitHub Actions .
- Служба GitHub Actions создает средство выполнения.
- Служба runner развертывает сетевой интерфейс карта сетевого интерфейса карта (сетевой адаптер) виртуальной сети Azure в GitHub.
- Агент runner выбирает задание рабочего процесса. Служба GitHub Actions очереди задания.
- Средство выполнения отправляет журналы обратно в службу GitHub Actions .
- Сетевой адаптер обращается к локальным ресурсам.
Сведения о поддерживаемых регионах
Служба GitHub Actions поддерживает подмножество всех регионов, которые предоставляет Azure. Чтобы упростить взаимодействие между службой GitHub Actions и подсетью, подсеть должна находиться в одном из следующих поддерживаемых регионов.
EastUsEastUs2WestUs2WestUs3CentralUsNorthCentralUsSouthCentralUsAustraliaEastJapanEastFranceCentralGermanyWestCentralNorthEuropeNorwayEastSwedenCentralSwitzerlandNorthUkSouthSoutheastAsia
Частная сеть Azure поддерживает запуски GPU в следующих регионах.
EastUsWestUsNorthCentralUsSouthCentralUs
Частная сеть Azure поддерживает запуски Arm64 в следующих регионах.
EastUsEastUs2WestUs2NorthCentralUsSouthCentralUs
Note
Gpu и arm64 runner в настоящее время находятся в бета-версии и подвержены изменению.
Если нужный регион не поддерживается, отправьте запрос на доступность нового региона в этой форме GitHub. Для подключения виртуальных сетей между регионами Azure также можно использовать пиринг глобальной виртуальной сети. Дополнительные сведения см. в документации по Azure.
Сведения о разрешениях службы GitHub Actions
Чтобы успешно развернуть сетевой адаптер и присоединить сетевой адаптер к подсети, служба GitHub Actions поддерживает следующие разрешения управления доступом на основе ролей Azure (RBAC) в подписке Azure. Дополнительные сведения об точном управлении доступом к ресурсам Azure см . в документации по Azure RBAC .
GitHub.Network/operations/readGitHub.Network/networkSettings/readGitHub.Network/networkSettings/writeGitHub.Network/networkSettings/deleteMicrosoft.Network/locations/operations/readMicrosoft.Network/locations/operationResults/readMicrosoft.Network/locations/usages/readMicrosoft.Network/networkInterfaces/readMicrosoft.Network/networkInterfaces/writeMicrosoft.Network/networkInterfaces/deleteMicrosoft.Network/networkInterfaces/join/actionMicrosoft.Network/networkSecurityGroups/join/actionMicrosoft.Network/networkSecurityGroups/readMicrosoft.Network/publicIpAddresses/readMicrosoft.Network/publicIpAddresses/writeMicrosoft.Network/publicIPAddresses/join/actionMicrosoft.Network/routeTables/join/actionMicrosoft.Network/virtualNetworks/readMicrosoft.Network/virtualNetworks/subnets/join/actionMicrosoft.Network/virtualNetworks/subnets/readMicrosoft.Network/virtualNetworks/subnets/writeMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/deleteMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/readMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/writeMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/details/readMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/validate/actionMicrosoft.Resources/subscriptions/resourceGroups/readMicrosoft.Resources/subscriptions/resourcegroups/deployments/readMicrosoft.Resources/subscriptions/resourcegroups/deployments/writeMicrosoft.Resources/subscriptions/resourcegroups/deployments/operations/readMicrosoft.Resources/deployments/readMicrosoft.Resources/deployments/writeMicrosoft.Resources/deployments/operationStatuses/read
Следующие разрешения будут представлены в двух корпоративных приложениях в клиенте Azure. После настройки частной сети Azure вы увидите корпоративные приложения клиента Azure.
GitHub CPS Network Serviceидентификатор:85c49807-809d-4249-86e7-192762525474GitHub Actions APIидентификатор:4435c199-c3da-46b9-a61d-76de3f2c9f82
Использование политик сети виртуальной сети
Так как сетевая карта runner, размещенная на основе GitHub, развертывается в виртуальной сети Azure, политики сети, применяемые к виртуальной сети, также применяются к средству выполнения.
Например, если виртуальная сеть настроена с помощью Azure ExpressRoute для предоставления доступа к локальным ресурсам (например, Artifactory) или подключена к VPN-туннелю для предоставления доступа к другим облачным ресурсам, эти политики доступа также применяются к модулям выполнения. Кроме того, применяются все правила исходящего трафика, применяемые к группе безопасности сети (NSG) виртуальной сети, что позволяет управлять исходящим доступом для пользователей.
Если вы включили мониторинг сетевых журналов для виртуальной сети, вы также можете отслеживать сетевой трафик для выполнения.
Управление политиками конфигурации сети для организаций в организации
Вы можете предоставить владелец организации в вашей организации возможность настраивать и поддерживать конфигурации сети уровня организации для GitHubразмещенных в ней средств выполнения.
Дополнительные сведения см. в разделе Настройка частной сети для размещенных на сайте GitHub средств выполнения в вашей организации.
Использование командлетов GitHub, размещенных в runners с виртуальной сетью Azure
Чтобы использовать GitHubразмещенных в среде runners с виртуальной сетью Azure, необходимо настроить ресурсы Azure, а затем создать сетевую конфигурацию в GitHub.
По умолчанию организации в организации не могут создавать новые конфигурации сети и наследовать только конфигурации сети корпоративного уровня. Владельцы предприятия могут задать политику, которая позволяет организациям в организации создавать конфигурации сети, которые не зависят от предприятия. Дополнительные сведения см. в разделе Настройка частной сети для размещенных на сайте GitHub средств выполнения в вашей организации.
Процедуры настройки частных сетей Azure на корпоративном уровне см. в разделе "Настройка частной сети для размещенных на сайте GitHub средств выполнения в вашей организации".
Процедуры настройки частных сетей Azure на уровне организации см. в разделе "Настройка частной сети для размещенных в GitHub runners в организации".