Acerca de la red privada de Azure para los ejecutores hospedados en GitHub
Puede utilizar los ejecutores hospedados en GitHub con una VNet de Azure Esto le permite utilizar la infraestructura administrada en GitHub para el CI/CD, a la vez que proporciona control total sobre las directivas de red de los ejecutores. Para más información sobre Azure VNET, consulta ¿Qué es Azure Virtual Network? en la documentación de Azure.
Puede conectar varias subredes VNET a GitHub.com y administrar el acceso a recursos privados para los ejecutores a través de grupos de ejecutores. Para más información acerca de los grupos de ejecutores, consulta "Control del acceso a los ejecutores más grandes."
El uso de ejecutores GitHub-hospedados dentro de Azure VNET permite realizar las siguientes acciones.
- Conecte de forma privada un ejecutor a los recursos dentro de una VNET de Azure sin abrir puertos de Internet, incluidos los recursos locales accesibles desde la VNet de Azure.
- Restringe a qué recursos pueden acceder, o conectarse a ellos, los ejecutores GitHub- hospedados con control total sobre las directivas de red salientes.
- Supervisa los registros de red de los ejecutores GitHub-hospedados y observa toda la conectividad hacia y desde un ejecutor.
Acerca del uso de ejecutores de mayor capacidad con la VNET de Azure
Se admiten ejecutores de Ubuntu y Windows 2-64 vCPU con la VNET de Azure. Para obtener más información acerca de los grupos de ejecutores, véase "Acerca de los ejecutores más grandes."
Las redes privadas para ejecutores hospedados en GitHub no son compatibles con direcciones IP estáticas para ejecutadores de mayor capacidad. Debe usar direcciones IP dinámicas, que es la configuración predeterminada para los ejecutadores de mayor capacidad. Para más información sobre conexiones en red para ejecutadores de mayor capacidad, véase "Acerca de los ejecutores más grandes".
Información sobre la comunicación de red
Para facilitar la comunicación entre las redes de GitHub y la VNet, una tarjeta de interfaz de red (NIC) hospedada en GitHub se despliega en su VNet de Azure.
Dado que la NIC reside dentro de la VNET, GitHub no pueden bloquear las conexiones entrantes. De manera predeterminada, las máquinas virtuales de Azure aceptarán conexiones entrantes de la misma VNET. Para más información, consulta AllowVNetInBound en Microsoft Learn. Se recomienda bloquear explícitamente todas las conexiones entrantes a los ejecutores. GitHub nunca requerirá conexiones entrantes a estas máquinas.
Una NIC permite que una máquina virtual (VM) de Azure se comunique con internet, Azure y los recursos en el entorno local. De este modo, toda la comunicación se mantiene privada dentro de los límites de red y las directivas de red aplicadas a la VNet también se aplican al ejecutor. Para más información sobre cómo administrar una interfaz de red, consulta Cambio de la configuración de la interfaz de red en Microsoft Learn.
Note
Es posible que aparezcan varias NIC para un único trabajo en la suscripción porque el servicio GitHub Actions sobreaprovisiona recursos para ejecutar trabajos. Una vez que un ejecutor está inactivo, el servicio GitHub Actions desaprovisiona automáticamente el recurso y elimina la NIC correspondiente.
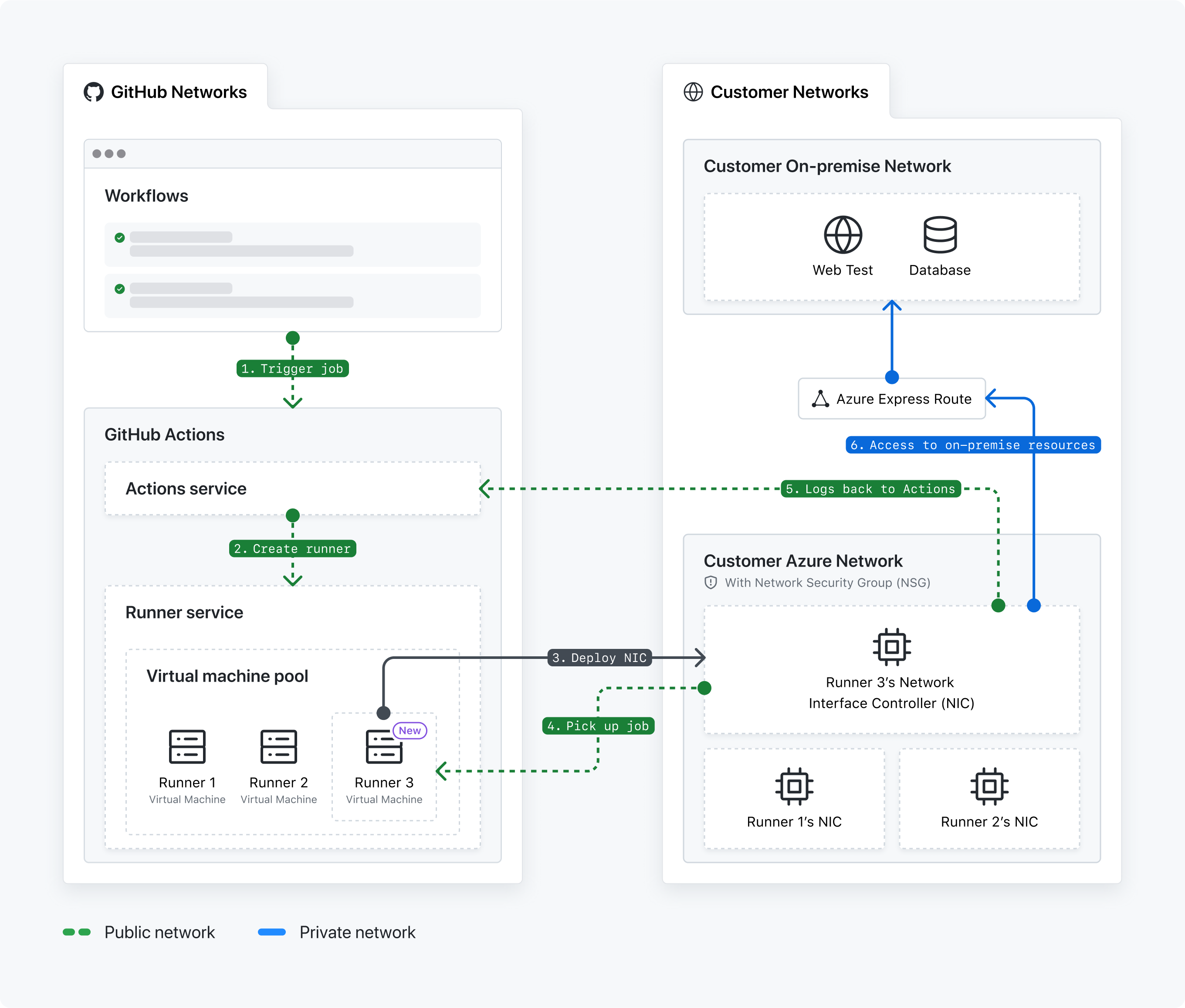
- Se activó un flujo de trabajo GitHub Actions.
- El servicio GitHub Actions crea un ejecutador.
- El servicio ejecutor implementa el ejecutor hospedado GitHub de la tarjeta de interfaz de red (NIC) en su Azure VNet.
- El agente ejecutor recoge la tarea del flujo de trabajo. El servicio GitHub Actions pone a la espera el trabajo.
- El ejecutor devuelve los registros al servicio GitHub Actions.
- La NIC accede a los recursos locales.
Acerca de la lista de regiones admitidas
El servicio GitHub Actions admite un subconjunto de todas las regiones que proporciona Azure. Para facilitar la comunicación entre el servicio GitHub Actions y la subred, la subred debe estar en una de las siguientes regiones admitidas.
EastUsEastUs2WestUs2WestUs3CentralUsNorthCentralUsSouthCentralUsAustraliaEastJapanEastFranceCentralGermanyWestCentralNorthEuropeNorwayEastSwedenCentralSwitzerlandNorthUkSouthSoutheastAsia
Las redes privadas de Azure admiten ejecutores de GPU en las siguientes regiones.
EastUsWestUsNorthCentralUsSouthCentralUs
Las redes privadas de Azure admiten ejecutores de ARM64 en las siguientes regiones.
EastUsEastUs2WestUs2NorthCentralUsSouthCentralUs
Note
Los ejecutores de ARM64 y GPU están actualmente en versión beta y están sujetos a cambios.
Si no se admite la región deseada, envía una solicitud de disponibilidad de región nueva en este formulario de GitHub. También puede usar el emparejamiento global de redes virtuales para conectar redes virtuales en distintas regiones de Azure. Para obtener más información, consulte Emparejamiento de redes virtuales en la documentación de Azure.
Acerca de los permisos del servicio GitHub Actions
Para implementar correctamente una NIC y unir una NIC a una subred, el servicio GitHub Actions mantiene los siguientes permisos de control de acceso basado en roles (RBAC) en la suscripción de Azure. Consulte la documentación de Azure sobre RBAC de Azure para obtener más información sobre la administración de accesos específicos de recursos de Azure.
GitHub.Network/operations/readGitHub.Network/networkSettings/readGitHub.Network/networkSettings/writeGitHub.Network/networkSettings/deleteMicrosoft.Network/locations/operations/readMicrosoft.Network/locations/operationResults/readMicrosoft.Network/locations/usages/readMicrosoft.Network/networkInterfaces/readMicrosoft.Network/networkInterfaces/writeMicrosoft.Network/networkInterfaces/deleteMicrosoft.Network/networkInterfaces/join/actionMicrosoft.Network/networkSecurityGroups/join/actionMicrosoft.Network/networkSecurityGroups/readMicrosoft.Network/publicIpAddresses/readMicrosoft.Network/publicIpAddresses/writeMicrosoft.Network/publicIPAddresses/join/actionMicrosoft.Network/routeTables/join/actionMicrosoft.Network/virtualNetworks/readMicrosoft.Network/virtualNetworks/subnets/join/actionMicrosoft.Network/virtualNetworks/subnets/readMicrosoft.Network/virtualNetworks/subnets/writeMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/deleteMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/readMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/writeMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/details/readMicrosoft.Network/virtualNetworks/subnets/serviceAssociationLinks/validate/actionMicrosoft.Resources/subscriptions/resourceGroups/readMicrosoft.Resources/subscriptions/resourcegroups/deployments/readMicrosoft.Resources/subscriptions/resourcegroups/deployments/writeMicrosoft.Resources/subscriptions/resourcegroups/deployments/operations/readMicrosoft.Resources/deployments/readMicrosoft.Resources/deployments/writeMicrosoft.Resources/deployments/operationStatuses/read
Los siguientes permisos estarán presentes en dos aplicaciones empresariales en el inquilino de Azure. Verá las aplicaciones empresariales de su inquilino de Azure después de configurar las redes privadas de Azure.
GitHub CPS Network Serviceid:85c49807-809d-4249-86e7-192762525474GitHub Actions APIid:4435c199-c3da-46b9-a61d-76de3f2c9f82
Uso de las directivas de red de la VNet
Dado que el ejecutor hospedado NIC GitHub se implementa en la VNet de Azure, las directivas de red aplicadas a la VNet también se aplican al ejecutor.
Por ejemplo, si la VNet está configurada con una instancia de Azure ExpressRoute para proporcionar acceso a recursos locales (pr ejemplo, artefactos), o conectada a un túnel VPN para proporcionar acceso a otros recursos basados en la nube, esas directivas de acceso también se aplican a los ejecutores. Además, las reglas de salida aplicadas al grupo de seguridad de red (NSG) de la VNet también se aplican, lo que le permite controlar el acceso saliente para los ejecutores.
Si ha habilitado la supervisión de registros de red para la VNet, también puede supervisar el tráfico de red de los ejecutores.
Administración de directivas de configuración de red para organizaciones en la empresa
Puedes conceder a los propietarios de la organización en tu empresa la capacidad de configurar y mantener configuraciones de red de nivel de organización para ejecutores hospedados en GitHub.
Para obtener más información, vea «Configuración de redes privadas para los ejecutores hospedados en GitHub en su empresa».
Uso de los ejecutores hospedados GitHub con una VNet de Azure
Para usar los ejecutores hospedados en GitHub con una VNET de Azure, deberá configurar los recursos de Azure y, a continuación, crear una configuración de red en GitHub.
De manera predeterminada, las organizaciones de una empresa no pueden crear configuraciones de red y solo heredan configuraciones de red de nivel empresarial. Los propietarios de empresas pueden establecer una directiva que permita a las organizaciones de la empresa crear configuraciones de red independientes de la empresa. Para obtener más información, vea «Configuración de redes privadas para los ejecutores hospedados en GitHub en su empresa».
Para conocer los procedimientos para configurar redes privadas de Azure en el nivel de empresa, consulta «Configuración de redes privadas para los ejecutores hospedados en GitHub en su empresa».
Para conocer los procedimientos para configurar redes privadas de Azure en el nivel de organización, consulta "Configuración de redes privadas para los ejecutores hospedados en GitHub en su organización".