커밋 서명 확인 정보
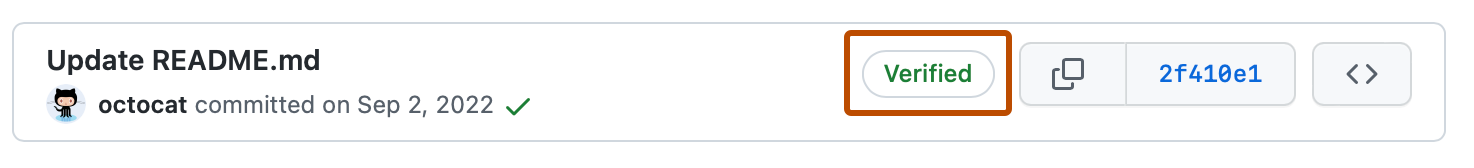
커밋 및 태그에 로컬로 서명하여 다른 사용자에게 변경 내용의 출처에 대한 확신을 줄 수 있습니다. 커밋 또는 태그에 암호화적으로 확인할 수 있는 GPG, SSH 또는 S/MIME 서명이 있는 경우 GitHub는 커밋 또는 태그 "Verified" 또는 "Partially verified"를 표시합니다.
대부분의 개별 사용자의 경우 GPG 또는 SSH가 커밋 서명에 가장 적합한 선택입니다. S/MIME 서명은 일반적으로 대규모 조직에서 필요합니다. SSH 서명은 가장 간단하게 생성할 수 있습니다. 기존 인증 키를 GitHub에 업로드하여 서명 키로 사용할 수도 있습니다. GPG 서명 키 생성은 SSH 키를 생성하는 것보다 더 복잡하지만 GPG에는 SSH에 없는 기능이 있습니다. GPG 키는 더 이상 사용되지 않을 때 만료되거나 철회될 수 있습니다. GPG 서명에는 만료 또는 해지되는 정보가 포함될 수 있습니다.
커밋과 태그는 경계 모드를 사용하도록 설정했는지 여부에 따라 다음과 같은 확인 상태를 갖습니다. 기본적으로 경계 모드는 사용하도록 설정되지 않습니다. 경계 모드를 사용하도록 설정하는 방법에 대한 자세한 내용은 모든 커밋에 대한 확인 상태 표시을(를) 참조하세요.
커밋 서명은 커밋 승인과 다릅니다. 커밋 서명에 관한 자세한 내용은 리포지토리에 대한 커밋 승인 정책 관리을(를) 참조하세요.
기본 상태
| Status | 설명 |
|---|---|
| 확인됨 | 커밋이 서명되고 서명이 성공적으로 확인되었습니다. |
| 미확인 | 커밋이 서명되었지만 서명을 확인할 수 없습니다. |
| 확인 상태 없음 | 커밋이 서명되지 않았습니다. |
영구 커밋 서명 확인
서명 선택(GPG, SSH, S/MIME)에 관계없이 커밋 서명이 확인되면 리포지토리의 네트워크 내에서 확인된 상태로 유지됩니다. 리포지토리 간 연결 이해을(를) 참조하세요.
GitHub에 푸시될 때 커밋 서명이 확인되면 확인 레코드가 커밋과 함께 저장됩니다. 이 레코드는 편집할 수 없으며 서명 키가 교체되거나 해지되거나 기여자가 조직을 떠나는 경우에도 서명이 시간이 지남에 따라 확인되도록 유지됩니다.
확인 레코드에는 확인이 완료되었을 때 타임스탬프 표시가 포함됩니다. 이 영구 레코드는 일관된 확인 상태를 보장하여 리포지토리 내에서 기여의 안정적인 기록을 제공합니다. GitHub에서 "Verified" 배지를 마우스로 가리키거나 verified_at 필드가 포함된 REST API를 통해 커밋에 액세스하여 이 타임스탬프를 볼 수 있습니다. 커밋에 대한 REST API 엔드포인트을(를) 참조하세요.
영구 커밋 서명 확인은 GitHub에 푸시된 새 커밋에 적용됩니다. 이 기능 이전의 모든 커밋의 경우 다음에 GitHub에서 커밋의 서명을 확인할 때 영구 레코드가 생성되므로 확인된 상태가 리포지토리의 기록 전체에서 안정적이고 신뢰할 수 있게 유지되도록 합니다.
해지 및 만료 후에도 레코드가 유지됩니다.
영구 커밋 서명 확인은 확인 시 커밋의 확인된 상태를 반영합니다. 즉, 서명 키가 나중에 해지, 만료, 변경된 경우 이전에 확인된 커밋은 초기 확인 중에 만든 레코드에 따라 확인된 상태를 유지합니다. GitHub는 키 상태의 변경에 따라 이전에 서명된 커밋을 다시 확인하거나 확인 상태를 소급하여 조정하지 않습니다. 조직에서는 보안 정책에 맞게 키 상태를 직접 관리해야 할 수 있습니다. 특히 자주 키 교체나 해지를 계획하는 경우 그렇습니다.
확인 레코드의 범위는 해당 리포지토리 네트워크로 지정됩니다.
확인 레코드는 리포지토리 네트워크에서 영구적입니다. 즉, 동일한 커밋이 동일한 리포지토리 또는 해당 포크로 다시 푸시되면 기존 확인 레코드가 다시 사용됩니다. 이렇게 하면 GitHub가 네트워크 내에 나타날 때마다 커밋을 다시 확인하지 않고도 관련 리포지토리에서 일관된 확인 상태를 유지할 수 있습니다. 이 지속성은 리포지토리 네트워크 내 커밋의 모든 인스턴스에서 커밋 신뢰성에 대해 통합되고 신뢰할 수 있는 보기를 강화합니다.
재지정 및 병합용 서명 확인
끌어오기 요청에서 다시 지정 및 병합 옵션을 사용하는 경우 커밋 서명 확인 없이 헤드 분기의 커밋이 기본 분기에 추가된다는 점에 유의해야 합니다. 이 옵션을 사용하면 GitHub는 원래 커밋의 데이터와 콘텐츠를 사용하여 수정된 커밋을 만듭니다. 즉, GitHub는 이 커밋을 실제로 만들지 않았으므로 일반 시스템 사용자로 서명할 수 없습니다. GitHub는 커밋자의 프라이빗 서명 키에 액세스할 수 없으므로 사용자를 대신하여 커밋에 서명할 수 없습니다.
이에 대한 해결 방법은 로컬로 다시 지정 및 병합한 다음 변경 내용을 끌어오기 요청의 기본 분기로 푸시하는 것입니다.
자세한 내용은 GitHub에서의 병합 메서드 정보을(를) 참조하세요.
경계 모드가 설정된 상태
| 상태 | 설명 |
|---|---|
| 확인됨 | 커밋이 서명되고 서명이 성공적으로 확인되었으며 커밋한 사람은 경계 모드를 활성화한 유일한 작성자입니다. |
| 부분적으로 확인됨 | 커밋이 서명되고 서명이 성공적으로 확인되었지만 커밋에 작성자가 있습니다. a) 커밋한 사람이 아니며 b) 경계 모드를 활성화했습니다. 이 경우 커밋 서명은 작성자의 동의를 보장하지 않으므로 커밋은 부분적으로만 확인됩니다. |
| 미확인 | 다음 중 하나는 true입니다. - 커밋이 서명되었지만 서명을 확인할 수 없습니다. - 커밋이 서명되지 않았고 커밋한 사람이 경계 모드를 활성화했습니다. - 커밋이 서명되지 않았고 작성자가 경계 모드를 활성화했습니다. |
리포지토리 관리자는 분기에 필요한 커밋 서명을 적용하여 서명 및 확인되지 않은 모든 커밋을 차단할 수 있습니다. 자세한 내용은 보호된 분기 정보을(를) 참조하세요.
GitHub에서 서명된 커밋 또는 태그의 확인 상태를 확인하고 커밋 서명이 확인되지 않은 이유를 확인할 수 있습니다. 자세한 내용은 커밋 및 태그 서명 확인 상태 확인을(를) 참조하세요.
GitHub은(는) 자동으로 GPG를 사용하여 웹 인터페이스를 사용하여 커밋에 서명합니다. GitHub이(가) 서명한 커밋은 확인된 상태가 됩니다. https://github.com/web-flow.gpg에서 사용할 수 있는 퍼블릭 키를 사용하여 로컬로 서명을 확인할 수 있습니다.
필요에 따라 GitHub GPG가 GitHub Codespaces에서 커밋에 서명하도록 선택할 수 있습니다. 코드스페이스에 대해 GPG 확인을 사용하도록 설정하는 방법에 대한 자세한 내용은 GitHub Codespaces 관련 GPG 확인 관리을(를) 참조하세요.
GPG 커밋 서명 확인
GPG를 사용하여 직접 생성하는 GPG 키를 사용하여 커밋에 서명할 수 있습니다.
GitHub는 OpenPGP 라이브러리를 사용하여 GitHub.com에서 계정에 추가한 퍼블릭 키에 대해 로컬로 서명된 커밋 및 태그를 암호화하여 확인할 수 있는지 확인합니다.
GPG를 사용하여 커밋에 서명하고 GitHub에서 해당 커밋을 확인하려면 다음 단계를 수행합니다.
SSH 커밋 서명 확인
SSH에서 직접 생성하는 SSH 키를 사용하여 커밋에 서명할 수 있습니다. 자세한 내용은 user.Signingkey에 대한 Git 참조 설명서를 참조하세요. 이미 SSH 키를 사용하여 GitHub로 인증한 경우 서명 키로 사용하기 위해 동일한 키를 다시 업로드할 수도 있습니다. 계정에 추가할 수 있는 서명 키의 개수에는 제한이 없습니다.
GitHub는 오픈 소스 Ruby 라이브러리인 ssh_data를 사용하여 GitHub.com에서 계정에 추가한 퍼블릭 키에 대해 로컬로 서명된 커밋 및 태그를 암호화하여 확인할 수 있는지 확인합니다.
Note
SSH 서명 확인은 Git 2.34 이상에서 사용할 수 있습니다. Git 버전을 업데이트하려면 Git 웹 사이트를 참조하세요.
SSH를 사용하여 커밋에 서명하고 GitHub에서 해당 커밋을 확인하려면 다음 단계를 수행합니다.
S/MIME 커밋 서명 확인
S/MIME를 사용하여 조직에서 발급한 X.509 키로 커밋에 서명할 수 있습니다.
GitHub는 Mozilla 브라우저에서 사용하는 것과 동일한 신뢰 저장소인 Debian ca-certificates 패키지를 사용하여 신뢰할 수 있는 루트 인증서의 퍼블릭 키에 대해 로컬로 서명된 커밋 및 태그를 암호화하여 확인할 수 있는지 확인합니다.
Note
S/MIME 서명 확인은 Git 2.19 이상에서 사용할 수 있습니다. Git 버전을 업데이트하려면 Git 웹 사이트를 참조하세요.
S/MIME를 사용하여 커밋에 서명하고 GitHub에서 해당 커밋을 확인하려면 다음 단계를 수행합니다.
퍼블릭 키를 GitHub에 업로드할 필요가 없습니다.
봇에 대한 서명 확인
커밋 서명이 필요한 조직 및 GitHub Apps은(는) 봇을 사용하여 커밋에 서명할 수 있습니다. 커밋 또는 태그에 암호화된 확인이 가능한 봇 서명이 있는 경우 GitHub는 커밋 또는 태그를 확인된 것으로 표시합니다.
요청이 GitHub App 또는 봇으로 확인 및 인증되고 사용자 지정 작성자 정보, 사용자 지정 커밋자 정보, 커밋 API와 같은 사용자 지정 서명 정보가 없는 경우에만 봇에 대한 서명 확인이 작동합니다.