You can configure two-factor authentication (2FA) using a TOTP app on mobile or desktop. After you have configured 2FA using a TOTP app, you can then also add security keys as alternate 2FA methods.
We strongly recommend using a time-based one-time password (TOTP) application to configure 2FA. Many TOTP apps support the secure backup of your authentication codes in the cloud and can be restored if you lose access to your device.
Warning:
- If you're a member or outside collaborator to a private repository of an organization that requires two-factor authentication, you must leave the organization before you can disable 2FA on your GitHub Enterprise Server instance.
- If you disable 2FA, you will automatically lose access to the organization and any private forks you have of the organization's private repositories. To regain access to the organization and your forks, re-enable two-factor authentication and contact an organization owner.
Configuring two-factor authentication using a TOTP app
A time-based one-time password (TOTP) application automatically generates an authentication code that changes after a certain period of time. These apps can be downloaded to your phone or desktop. We recommend using cloud-based TOTP apps. GitHub is app-agnostic when it comes to TOTP apps, so you have the freedom to choose any TOTP app you prefer. Just search for TOTP app in your browser to find various options. You can also refine your search by adding keywords like free or open source to match your preferences.
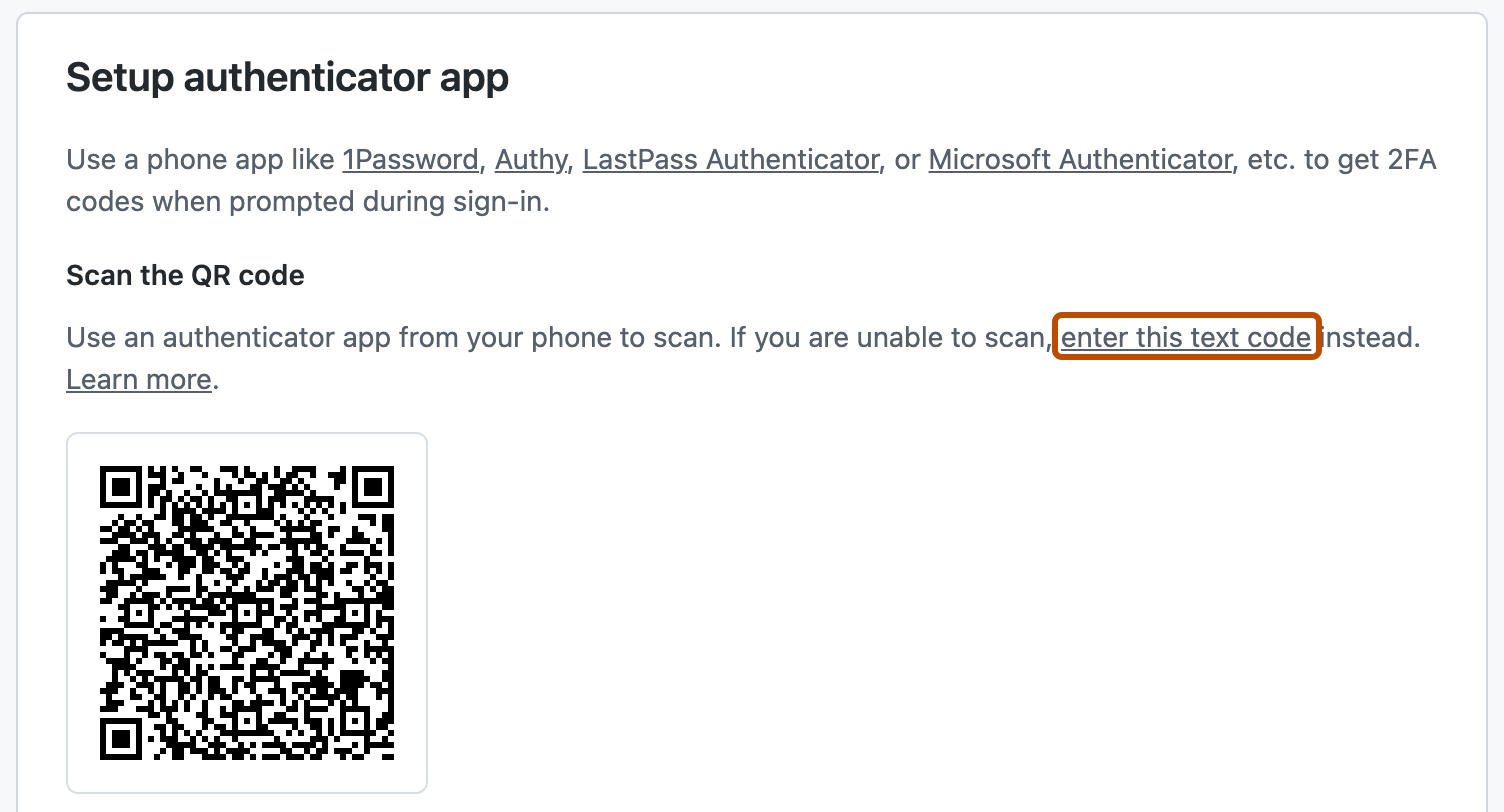
Tip: To configure authentication via TOTP on multiple devices, during setup, scan the QR code using each device at the same time or save the "text code", which is the TOTP secret. If 2FA is already enabled and you want to add another device, you must re-configure your TOTP app from your security settings.
-
Download a TOTP app of your choice to your phone or desktop.
-
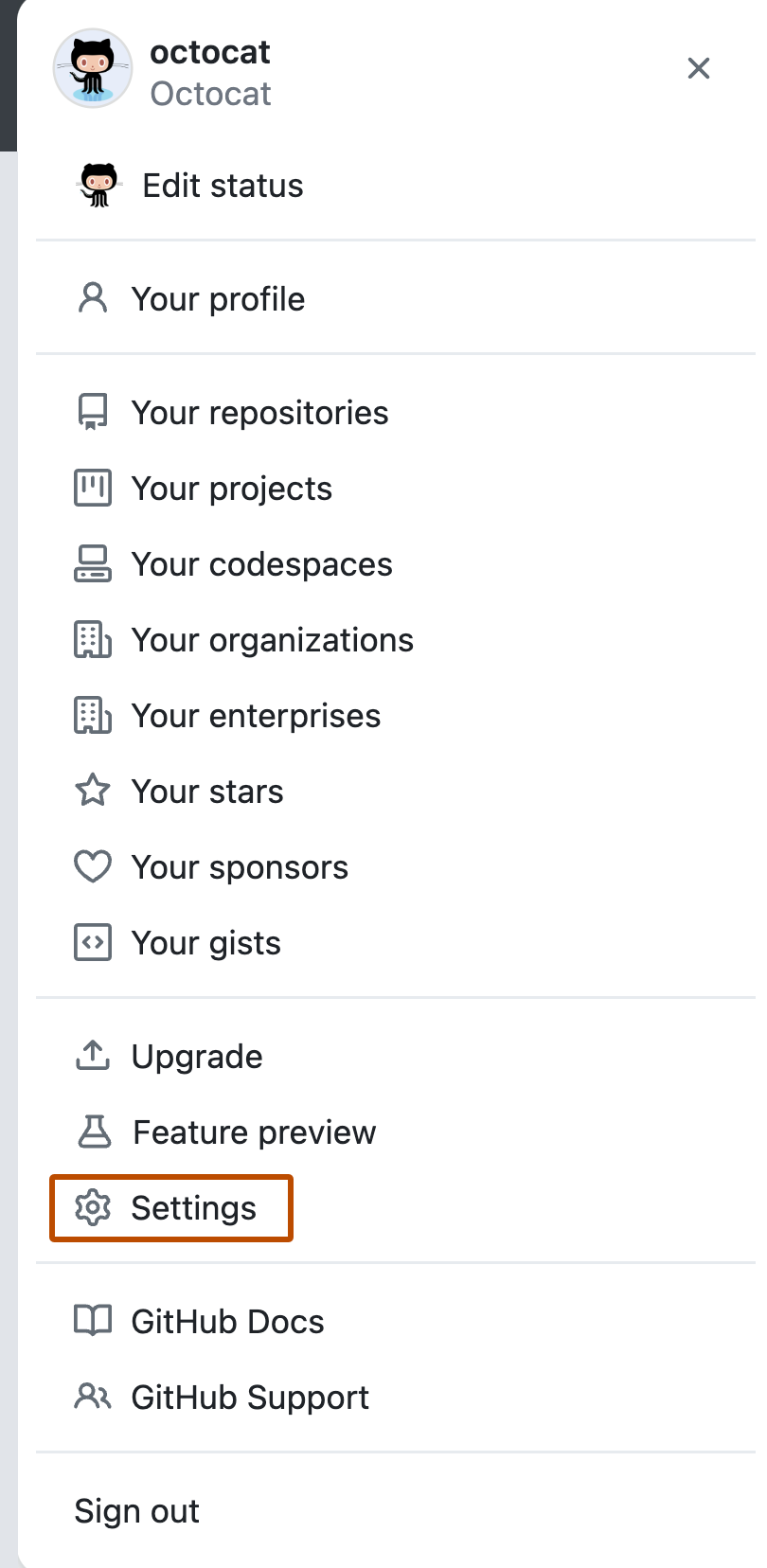
In the upper-right corner of any page, click your profile photo, then click Settings.
-
In the "Access" section of the sidebar, click Password and authentication.
-
In the "Two-factor authentication" section of the page, click Enable two-factor authentication.
-
Under "Two-factor authentication", select Set up using an app and click Continue.
-
Under "Authentication verification", do one of the following:
- Scan the QR code with your mobile device's app. After scanning, the app displays a six-digit code that you can enter on GitHub Enterprise Server.
- If you can't scan the QR code, click enter this text code to see a code that you can manually enter in your TOTP app instead.
-
The TOTP application saves your account on your GitHub Enterprise Server instance and generates a new authentication code every few seconds. On GitHub Enterprise Server, type the code into the field under "Enter the six-digit code from the application".
-
After you've saved your recovery codes and enabled 2FA, we recommend you sign out and back in to your account. In case of problems, such as a forgotten password or typo in your email address, you can use recovery codes to access your account and correct the problem.
-
Under "Save your recovery codes", click Download to download your recovery codes to your device. Save them to a secure location because your recovery codes can help you get back into your account if you lose access.
-
After saving your two-factor recovery codes, click I have saved my recovery codes to enable two-factor authentication for your account.
-
Optionally, you can configure additional 2FA methods to reduce your risk of account lockout. For more details on how to configure each additional method, see "Configuring two-factor authentication using GitHub Mobile" and "Configuring two-factor authentication using a security key".
Manually configuring a TOTP app
If you are unable to scan the setup QR code or wish to setup a TOTP app manually and require the parameters encoded in the QR code, they are:
- Type:
TOTP - Label:
GitHub:<username>where<username>is your handle on GitHub, for examplemonalisa - Secret: This is the encoded setup key, shown if you click "Enter this text code" during configuration
- Issuer:
GitHub - Algorithm: The default of SHA1 is used
- Digits: The default of 6 is used
- Period: The default of 30 (seconds) is used
Configuring two-factor authentication using a security key
On most devices and browsers, you can use a physical security key over USB or NFC. Most browsers can use the fingerprint reader, facial recognition, or password/PIN on your device as a security key as well.
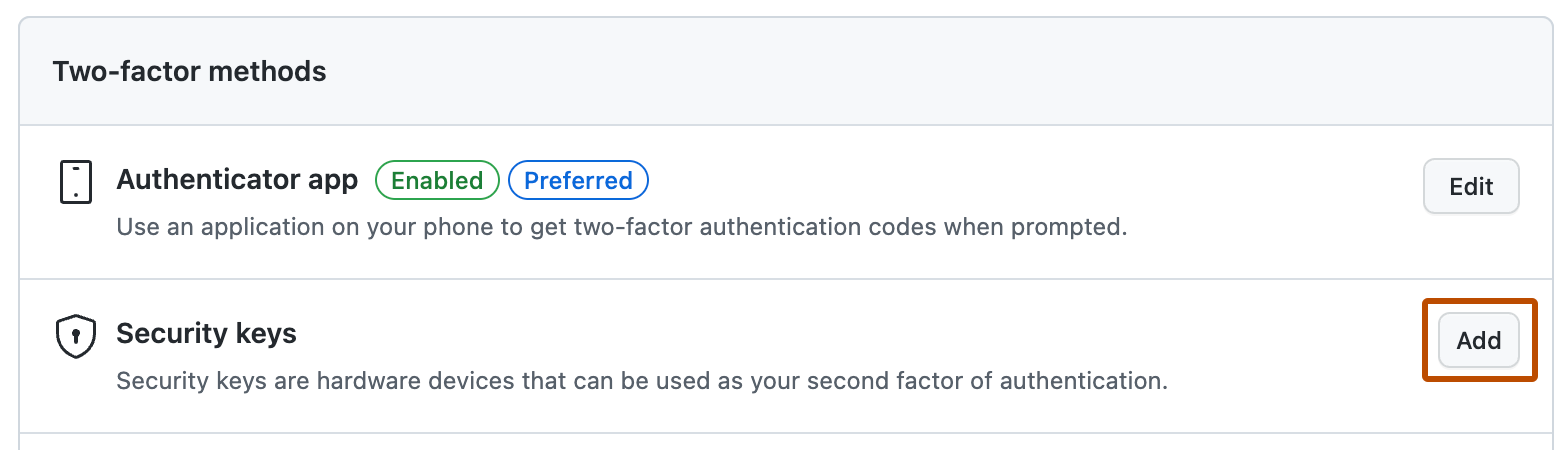
Registering a security key for your account is available after enabling 2FA with a TOTP application. If you lose your security key, you'll still be able to use your phone's code to sign in.
-
You must have already configured 2FA via a TOTP mobile app.
-
Ensure that you have a WebAuthn compatible security key inserted into your device.
-
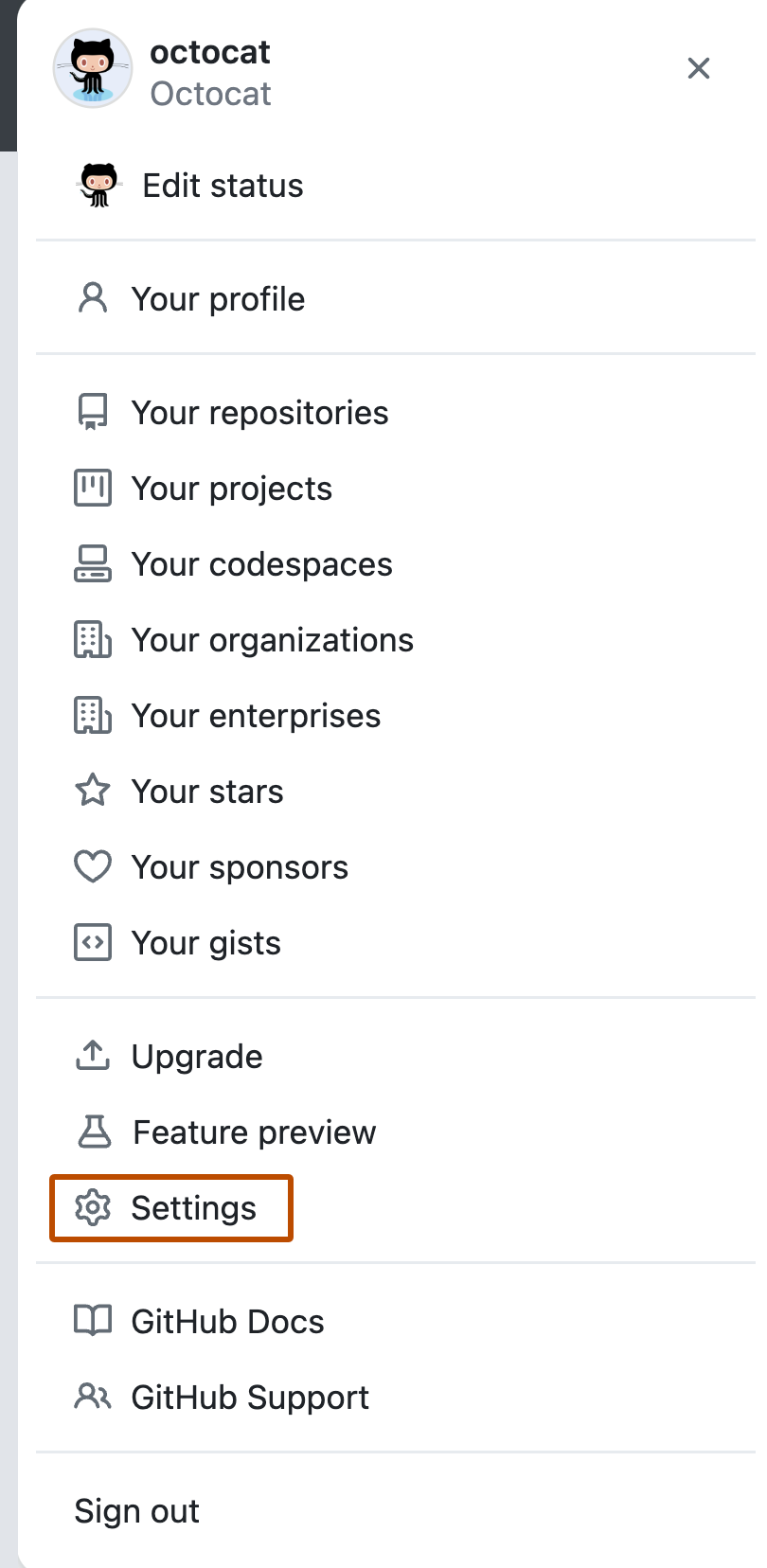
In the upper-right corner of any page, click your profile photo, then click Settings.
-
In the "Access" section of the sidebar, click Password and authentication.
-
Next to "Security keys", click Add.
-
Under "Security keys", click Register new security key.
-
Type a nickname for the security key, then click Add.
-
Following your security key's documentation, activate your security key.
-
Confirm that you've downloaded and can access your recovery codes. If you haven't already, or if you'd like to generate another set of codes, download your codes and save them in a safe place. For more information, see "Configuring two-factor authentication recovery methods."
-
After you've saved your recovery codes and enabled 2FA, we recommend you sign out and back in to your account. In case of problems, such as a forgotten password or typo in your email address, you can use recovery codes to access your account and correct the problem.