Preguntar GitHub Copilot Chat sobre las alertas code scanning
Con una licencia de GitHub Copilot para grandes empresas, puede solicitar ayuda a Copilot Chat para comprender mejor las alertas de seguridad, incluidas las alertas de code scanning, en los repositorios de su organización. Para más información, consulta Preguntas a GitHub Copilot en GitHub.
Generación de correcciones sugeridas para las alertas de code scanning
Autocorrección de GitHub Copilot puede generar correcciones para las alertas identificadas por el análisis de code scanning. Se admiten la mayoría de los tipos de alertas de CodeQL y también algunas alertas de herramientas de terceros. Para más información, consulta Uso responsable de Copilot Autofix para el análisis de código.
Nota:
No necesita una suscripción a GitHub Copilot para usar . está disponible para todos los repositorios públicos en GitHub.com, así como repositorios internos o privados que pertenecen a organizaciones y empresas que tienen una licencia para GitHub Code Security.
- En GitHub, navegue hasta la página principal del repositorio.
- En el nombre del repositorio, haz clic en Seguridad. Si no puedes ver la pestaña "Seguridad", selecciona el menú desplegable y, a continuación, haz clic en Seguridad.

- En la barra lateral izquierda, haz clic en Code scanning.
- Haga clic en el nombre de una alerta.
- Si Autocorrección de Copilot puede sugerir una corrección, en la parte superior de la página, haz clic en Generate fix.
- Una vez generada la corrección sugerida, en la parte inferior de la página, puede hacer clic en Crear solicitud de incorporación de cambios con corrección para generar automáticamente una solicitud de incorporación de cambios con la corrección sugerida. Se crea una nueva rama a partir de la rama predeterminada, se confirma la corrección generada y se crea un borrador de solicitud de cambios. Puede probar y editar la corrección sugerida como lo haría con cualquier otra corrección.
También puede usar la Autocorrección de API para puntos de conexión de alertas históricas para generar, obtener y confirmar correcciones sugeridas.
- Crear un autofijo para una alerta de examen de código
- Obtener el estado de un autofijo para una alerta de análisis de código
- Confirmar un autofijo para una alerta de examen de código
Para obtener información sobre las limitaciones de las correcciones generadas automáticamente, consulta Limitaciones de las sugerencias.
Corrección de una alerta manually
Cualquiera con permisos de escritura en un repositorio puede arreglar una alerta si confirma una corrección en el código. Si el repositorio tiene programado un code scanning para ejecutarse en las solicitudes de cambios, es mejor levantar una solicitud de cambios con tu corrección. Esto activará el análisis del code scanning en los cambios y probará que tu arreglo no introduciría ningún problema nuevo. Para más información, consulta Clasificar las alertas del escaneo de código en las solicitudes de cambios.
Puedes usar la búsqueda de texto libre o los filtros para mostrar un subconjunto de alertas y, después, marcar como cerradas todas las alertas que coincidan.
Las alertas pueden arreglarse en una rama pero no en alguna otra. Puedes utilizar el filtro "Branch" en el resumen de las alertas para verificar si una alerta está fija en una rama particular.

Tenga en cuenta que si ha filtrado las alertas en una rama no predeterminada, pero las mismas alertas existen en la rama predeterminada, en la página de alertas de cualquier alerta se seguirá reflejando el estado de la alerta en la rama predeterminada, incluso si ese estado entra en conflicto con el de una rama no predeterminada. Por ejemplo, una alerta que aparece en la lista "Abrir" en el resumen de alertas para branch-x podría mostrar un estado de "Corregido" en la página de alertas, si ya se ha corregido en la rama predeterminada. Puede ver el estado de la alerta de la rama filtrada en la sección Ramas afectadas del lado derecho de la página de alertas.
Nota:
Si ejecutas code scanning con varias configuraciones, a veces más de una configuración generará la misma alerta. A menos que ejecutes todas las configuraciones con regularidad, es posible que veas alertas que se han corregido en una configuración, pero no en otra. Estas configuraciones y alertas obsoletas se pueden quitar de una rama. Para más información, consulta Eliminación de configuraciones y alertas obsoletas de una rama.
Descartar alertas
Hay dos formas de cerrar una alerta. Puedes arreglar el problema en el código, o puedes descartar la alerta.
Descartar una alerta es una manera de cerrar una alerta que considere que no es necesario solucionar. Por ejemplo, un error en el código que se utiliza únicamente para hacer pruebas, o cuando el esfuerzo de areglar el error es mayor que el beneficio potencial de mejorar el código. Puede eliminar alertas desde las anotaciones de code scanning en el código, o bien desde la lista de resumen dentro de la pestaña Seguridad.
Cuando descartas una alerta:
- Se descarta en todas las ramas.
- La alerta se elimina de la cantidad de alertas actuales para tu proyecto.
- La alerta se mueve a la lista de "Cerrado" en el resumen de alertas, desde donde puedes volver a abrirla en caso de que lo necesites.
- Se registra el motivo por el que cerró la alerta.
- Opcionalmente, puedes comentar un descarte para registrar el contexto del descarte de una alerta.
- La siguiente vez que se ejecute el code scanning, este código no volverá a generar una alerta.
Para descartar alertas:
-
En GitHub, navegue hasta la página principal del repositorio.
-
En el nombre del repositorio, haz clic en Seguridad. Si no puedes ver la pestaña "Seguridad", selecciona el menú desplegable y, a continuación, haz clic en Seguridad.

-
En la barra lateral izquierda, haz clic en Code scanning.
-
Si quieres descartar una alerta, es importante explorarla primero para que puedas elegir la razón correcta para descartarla. Da clic en la alerta que quisieras explorar.
-
Revisa la alerta y, después, haz clic en Descartar alertar y elige un motivo para cerrar la alerta.
Es importante elegir la razón adecuada del menú desplegable, ya que esto puede afectar si la consulta continuará incluyéndose en los análisis futuros. Opcionalmente, puede comentar un descarte para registrar el contexto del descarte de una alerta. El comentario de descarte se agrega a la escala de tiempo de la alerta y se puede usar como justificación durante el proceso de auditoría y creación de informes. Puedes recuperar o establecer un comentario mediante la API REST de examen de código. El comentario se incluye en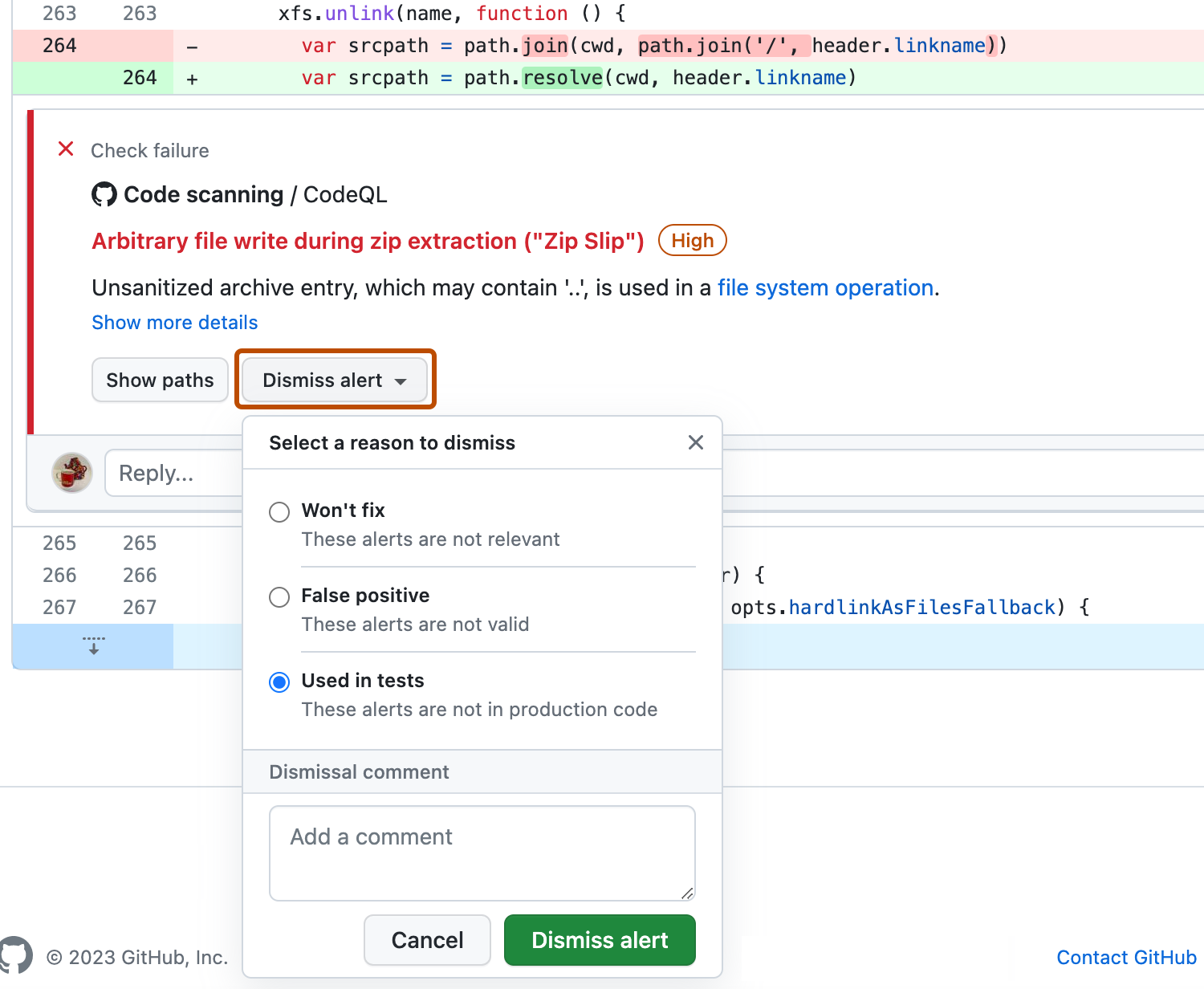
dismissed_commentpara el punto de conexiónalerts/{alert_number}. Para más información, consulta Puntos de conexión de la API de REST para el análisis de código.Si descartas una alerta de CodeQL como consecuencia de un resultado de falso positivo, por ejemplo, porque el código utiliza una biblioteca de sanitización que no es compatible, considera contribuir con el repositorio de CodeQL y mejorar el análisis. Para más información sobre CodeQL, consulta Contribución a CodeQL.
Descartar varias alertas al mismo tiempo
Si un proyecto tiene varias alertas que quieras descartar por la misma razón, puedes descartarlas por lote desde el resúmen de las alertas. Habitualmente quieres filtrar la lista y luego descartar todas las alertas coincidentes. Por ejemplo, puede que quieras descartar todas las alertas actuales del proyecto que se hayan etiquetado para una vulnerabilidad de Enumeración de Debilidades (CWE, por sus siglas en inglés) Común en particular.
Volver a abrir alertas descartadas
Si descartas una alerta, pero más adelante te das cuenta de que necesitas corregir la alerta, puedes volver a abrirla y corregir el problema con el código. Muestra la lista de alertas cerradas, busca la alerta, muéstrala y vuelve a abrirla. A continuación, puedes corregir la alerta de la misma manera que cualquier otra alerta.
Eliminación de configuraciones y alertas obsoletas de una rama
Es posible que tengas varias configuraciones de examen de código en un único repositorio. Cuando se ejecutan, varias configuraciones pueden generar la misma alerta. Además, si las configuraciones se ejecutan en diferentes programaciones, los estados de alerta pueden quedar obsoletos para configuraciones poco frecuentes u obsoletas. Para más información sobre las alertas de varias configuraciones, consulta Acerca de las alertas de análisis de código.
-
En GitHub, navegue hasta la página principal del repositorio.
-
En el nombre del repositorio, haz clic en Seguridad. Si no puedes ver la pestaña "Seguridad", selecciona el menú desplegable y, a continuación, haz clic en Seguridad.

-
En la barra lateral izquierda, haz clic en Code scanning.
-
En "Code scanning", haz clic en una alerta de code scanning.
-
En la sección "Ramas afectadas" de la barra lateral, haz clic en la rama deseada.
-
En el cuadro de diálogo "Análisis de configuraciones", revisa los detalles de las configuraciones que han notificado esta alerta en la rama seleccionada. Para eliminar una configuración no deseada de la rama deseada, haz clic en .
Si eliminas una configuración por error, haz clic en Cancelar para evitar aplicar los cambios.

-
Una vez que hayas quitado las configuraciones no deseadas y hayas confirmado que se muestran las configuraciones esperadas, haz clic en Guardar cambios.
Si guardas los cambios después de eliminar accidentalmente una configuración, vuelve a ejecutar la configuración para actualizar la alerta. Para más información sobre cómo volver a configuraciones en las que se usa GitHub Actions, consulta Volver a ejecutar flujos de trabajo y jobs.
Nota:
- Si quitas todas las configuraciones de code scanning para la rama predeterminada del repositorio, esta permanecerá en la barra lateral "Ramas afectadas", pero no la analizará ninguna configuración.
- Si quitas todas las configuraciones de code scanning de cualquier rama que no sea la predeterminada del repositorio, esa rama se quitará de la barra lateral "Ramas afectadas".