You can configure your GitHub Enterprise instance to require SSL connections by following the instructions below.
Configuration
-
Take a snapshot of your VM.
Tip: As with most setting changes, we highly recommend you take a VM snapshot prior to saving. That way, if something goes wrong, you can revert your VM to the state it was in before you made any changes.
Sign into your Enterprise instance as an admin user.
-
Access your Management Console's Settings page at:
http(s)://<em>hostname</em>/setup/settings Click the Privacy tab.

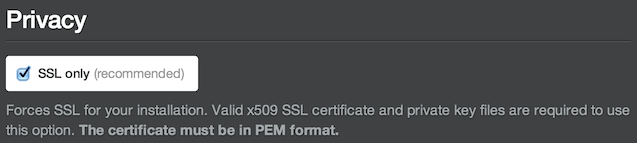
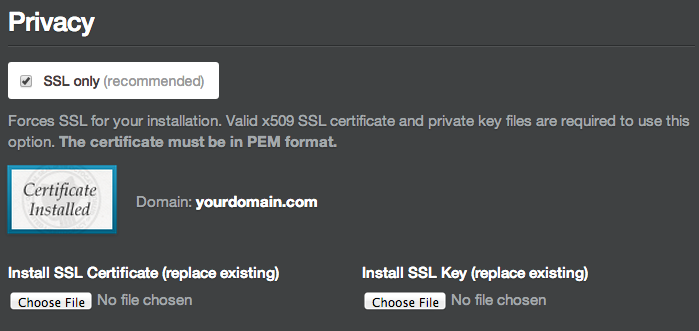
Enable the SSL only option.
Choose an SSL certificate—in PEM format—to install. This file will usually have a
.pem,.crt, or.cerextension.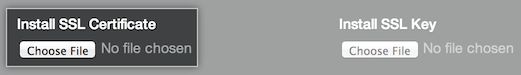
-
Choose an SSL key—in PEM format—to install. This file will usually have a
.keyextension.
Warning: The key must not have a passphrase!
Click the Save settings button at the bottom of the page. If both the certificate and key are accepted, you'll return to the settings page after the configuration process completes.
Troubleshooting
I need to remove the passphrase from my key file
If you have a Linux machine with OpenSSL installed, you can accomplish this in two steps:
-
Rename your original key file:
mv yourdomain.key yourdomain.key.orig -
Generate a new key without a passphrase:
openssl rsa -in yourdomain.key.orig -out yourdomain.keyNote that you'll be prompted for the key's passphrase when you run this command.
I need to convert my certificate or key into PEM format
You can convert your certificate into PEM format using this tool.
You should be able to convert your key into PEM format using the openssl command. For example, you can convert a key from DER format into PEM format as follows:
openssl rsa -in yourdomain.der -inform DER -out yourdomain.key -outform PEM
If you need help, feel free to contact support.
I uploaded my key and now my install is unresponsive
GitHub Enterprise has a number of safeguards to prevent this from happening, but if you find yourself in this situation please contact support with specific details about what you've done. It would be helpful if you included a copy of your certificate.
We'll do everything we can to help get your install running again as quickly as possible.
My programs are throwing certificate validity errors
Clients, such as web browsers and command-line Git, will throw an error if they cannot verify the validity of a certificate. This often occurs with self-signed certificates as well as "chained root" certificates issued off of an intermediate root certificate that is not recognized by the client.
If you are using a certificate signed by a certificate authority (CA), the certificate file that you upload to GitHub Enterprise must include a certificate chain with that CA's root certificate. To create such a file, concatenate your entire certificate chain (or "certificate bundle") onto the end of your certificate—ensuring that the principle certificate with your hostname comes first. On most systems you can do this with a command similar to the following:
cat yourdomain.com.crt bundle-certificates.crt > yourdomain.combined.crt
You should be able to download a certificate bundle (e.g. bundle-certificates.crt) from your certificate authority or SSL vendor.
