Note: Your site administrator must set up Dependabot updates for your GitHub Enterprise Server instance before you can use this feature. For more information, see "Enabling Dependabot for your enterprise."
Your repository's Dependabot alerts tab lists all open and closed Dependabot alerts and corresponding Dependabot security updates. You can filter alerts by package, ecosystem, or manifest. You can sort the list of alerts, and you can click into specific alerts for more details. You can also dismiss or reopen alerts. For more information, see "About Dependabot alerts."
You can enable automatic security updates for any repository that uses Dependabot alerts and the dependency graph. For more information, see "About Dependabot security updates."
About updates for vulnerable dependencies in your repository
GitHub Enterprise Server generates Dependabot alerts when we detect that the default branch of your codebase is using dependencies with known security risks. For repositories where Dependabot security updates are enabled, when GitHub Enterprise Server detects a vulnerable dependency in the default branch, Dependabot creates a pull request to fix it. The pull request will upgrade the dependency to the minimum possible secure version needed to avoid the vulnerability.
Each Dependabot alert has a unique numeric identifier and the Dependabot alerts tab lists an alert for every detected vulnerability. Legacy Dependabot alerts grouped vulnerabilities by dependency and generated a single alert per dependency. If you navigate to a legacy Dependabot alert, you will be redirected to a Dependabot alerts tab filtered for that package.
You can filter and sort Dependabot alerts using a variety of filters and sort options available on the user interface. For more information, see "Prioritizing Dependabot alerts" below.
You can also audit actions taken in response to Dependabot alerts. For more information, see "Auditing security alerts."
Prioritizing Dependabot alerts
GitHub helps you prioritize fixing Dependabot alerts.
Viewing Dependabot alerts
You can view all open and closed Dependabot alerts and corresponding Dependabot security updates in your repository's Dependabot alerts tab. You can sort and filter Dependabot alerts by selecting a filter from the dropdown menu.
To view summaries of alerts for all or a subset of repositories owned by your organization, use security overview. For more information, see "About security overview."
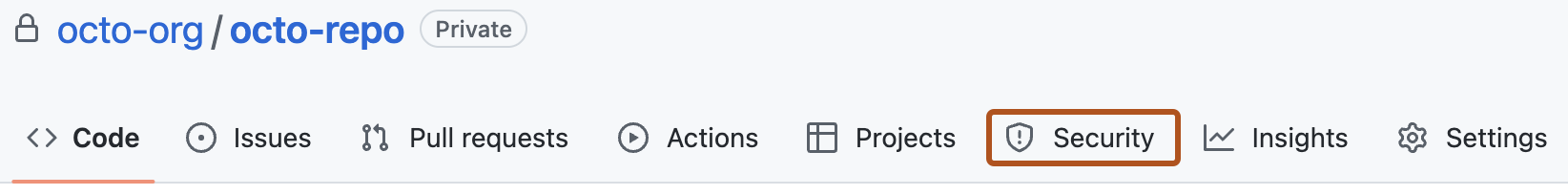
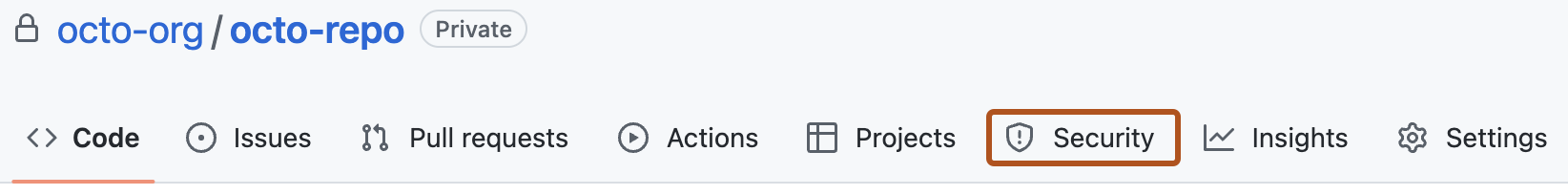
- On your GitHub Enterprise Server instance, navigate to the main page of the repository.
- Under the repository name, click Security. If you cannot see the "Security" tab, select the dropdown menu, and then click Security.
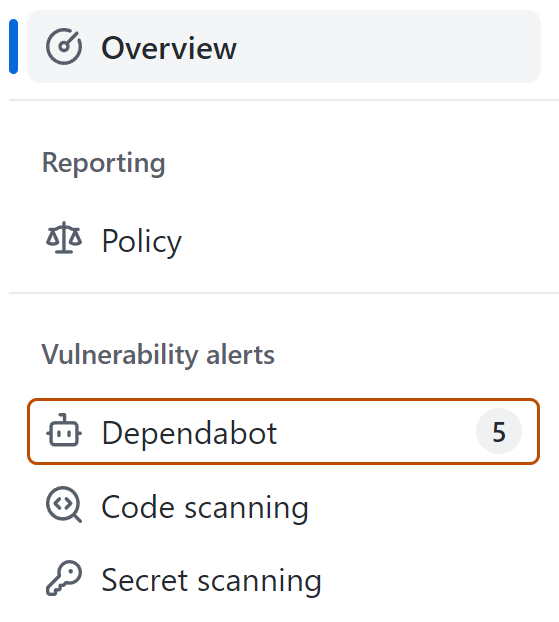
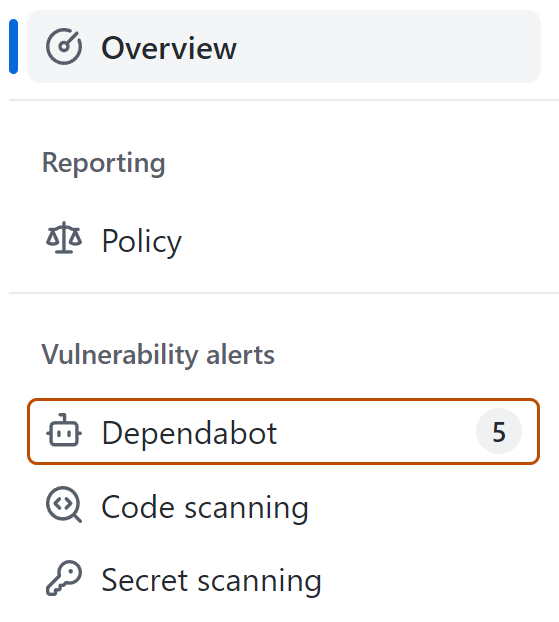
- In the "Vulnerability alerts" sidebar of security overview, click Dependabot. If this option is missing, it means you don't have access to security alerts and need to be given access. For more information, see "Managing security and analysis settings for your repository."
- Optionally, to filter alerts, select a filter in a dropdown menu then click the filter that you would like to apply. You can also type filters into the search bar. For more information about filtering and sorting alerts, see "Prioritizing Dependabot alerts."
- Click the alert that you would like to view.
Reviewing and fixing alerts
It’s important to ensure that all of your dependencies are clean of any security weaknesses. When Dependabot discovers vulnerabilities in your dependencies, you should assess your project’s level of exposure and determine what remediation steps to take to secure your application.
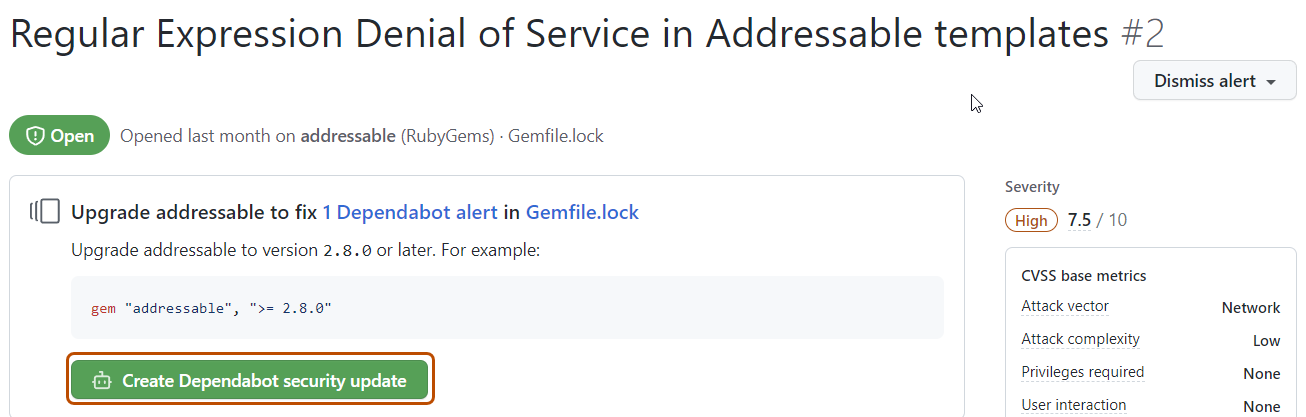
If a patched version of the dependency is available, you can generate a Dependabot pull request to update this dependency directly from a Dependabot alert. If you have Dependabot security updates enabled, the pull request may be linked in the Dependabot alert.
In cases where a patched version is not available, or you can’t update to the secure version, Dependabot shares additional information to help you determine next steps. When you click through to view a Dependabot alert, you can see the full details of the security advisory for the dependency including the affected functions. You can then check whether your code calls the impacted functions. This information can help you further assess your risk level, and determine workarounds or if you’re able to accept the risk represented by the security advisory.
Fixing vulnerable dependencies
-
View the details for an alert. For more information, see "Viewing Dependabot alerts" (above).
-
If you have Dependabot security updates enabled, there may be a link to a pull request that will fix the dependency. Alternatively, you can click Create Dependabot security update at the top of the alert details page to create a pull request.
-
Optionally, if you do not use Dependabot security updates, you can use the information on the page to decide which version of the dependency to upgrade to and create a pull request to update the dependency to a secure version.
-
When you're ready to update your dependency and resolve the vulnerability, merge the pull request.
Each pull request raised by Dependabot includes information on commands you can use to control Dependabot. For more information, see "Managing pull requests for dependency updates."
Dismissing Dependabot alerts
Tip: You can only dismiss open alerts.
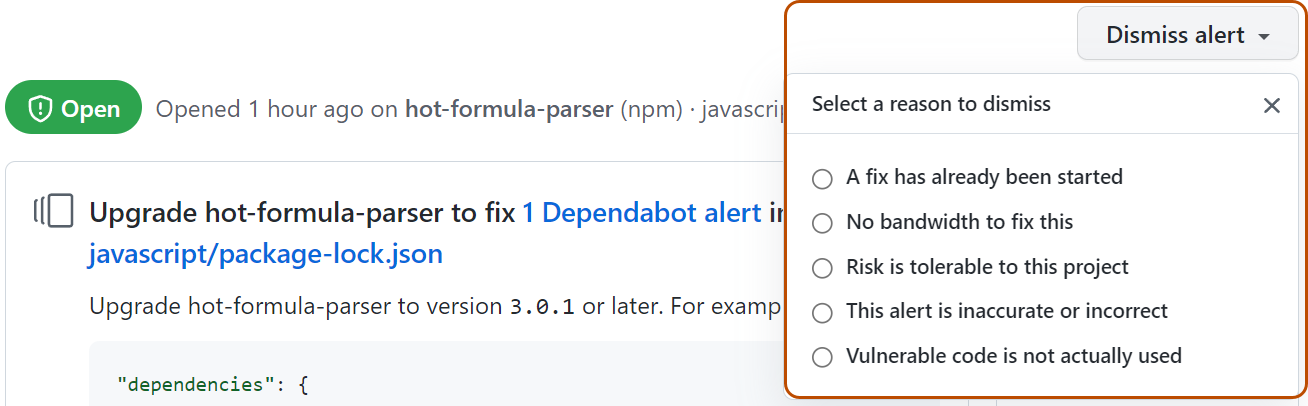
If you schedule extensive work to upgrade a dependency, or decide that an alert does not need to be fixed, you can dismiss the alert. Dismissing alerts that you have already assessed makes it easier to triage new alerts as they appear.
-
View the details for an alert. For more information, see "Viewing vulnerable dependencies" (above).
-
Select the "Dismiss" dropdown, and click a reason for dismissing the alert. Unfixed dismissed alerts can be reopened later.
Viewing and updating closed alerts
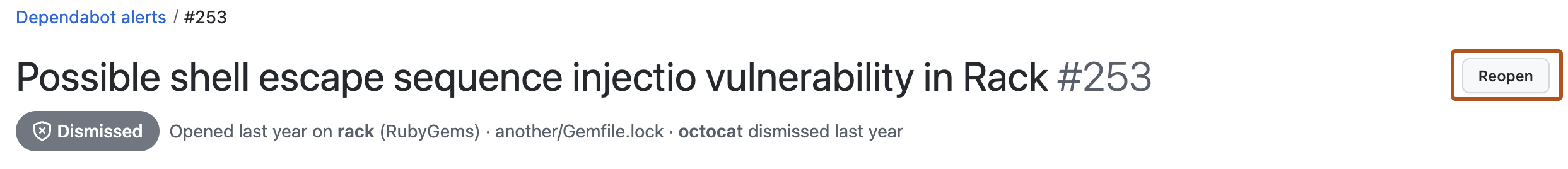
You can view all open alerts, and you can reopen alerts that have been previously dismissed. Closed alerts that have already been fixed cannot be reopened.
-
On your GitHub Enterprise Server instance, navigate to the main page of the repository.
-
Under the repository name, click Security. If you cannot see the "Security" tab, select the dropdown menu, and then click Security.
-
In the "Vulnerability alerts" sidebar of security overview, click Dependabot. If this option is missing, it means you don't have access to security alerts and need to be given access. For more information, see "Managing security and analysis settings for your repository."
-
To just view closed alerts, click Closed.
-
Click the alert that you would like to view or update.
-
Optionally, if the alert was dismissed and you wish to reopen it, click Reopen. Alerts that have already been fixed cannot be reopened.
Reviewing the audit logs for Dependabot alerts
When a member of your organization or enterprise performs an action related to Dependabot alerts, you can review the actions in the audit log. For more information about accessing the log, see "Reviewing the audit log for your organization" and "Accessing the audit log for your enterprise."
Events in your audit log for Dependabot alerts include details such as who performed the action, what the action was, and when the action was performed. For information on the Dependabot alerts actions, see the repository_vulnerability_alert category in "Audit log events for your organization" and "Audit log events for your enterprise."