Enabling secret scanning alerts for users
You can enable secret scanning alerts for users for any repository that is owned by an organization, and for repositories owned by user accounts when using GitHub Enterprise Cloud with Enterprise Managed Users. Once enabled, secret scanning scans for any secrets in your entire Git history on all branches present in your GitHub repository. Additionally, secret scanning scans:
- Descriptions and comments in issues
- Titles, descriptions, and comments, in open and closed historical issues. A notification is sent to the relevant partner when a historical partner pattern is detected.
- Titles, descriptions, and comments in pull requests
- Titles, descriptions, and comments in GitHub Discussions
- Wikis
This additional scanning is free for public repositories.
Note: The scanning of content in pull requests, GitHub Discussions, and wikis is currently in beta and subject to change.
You can also enable secret scanning for multiple repositories in an organization at the same time. For more information, see "Quickstart for securing your organization."
Note: If your organization is owned by an enterprise account, an enterprise owner can also enable secret scanning at the enterprise level. For more information, see "Managing GitHub Advanced Security features for your enterprise."
A repository administrator can choose to disable secret scanning for a repository at any time. For more information, see "Managing security and analysis settings for your repository."
-
On GitHub.com, navigate to the main page of the repository.
-
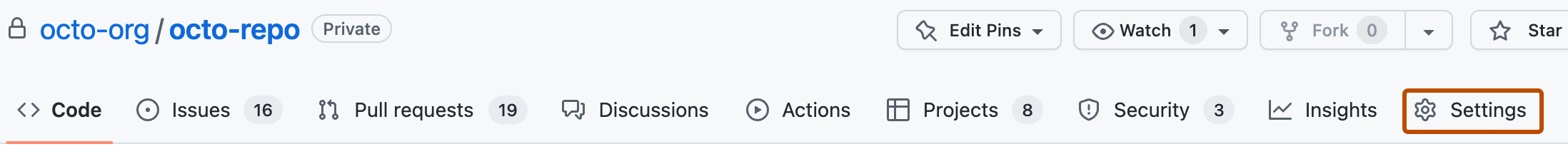
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Code security and analysis.
-
If Advanced Security is not already enabled for the repository, to the right of "GitHub Advanced Security", click Enable.
-
Review the impact of enabling Advanced Security, then click Enable GitHub Advanced Security for this repository.
-
When you enable Advanced Security, secret scanning may automatically be enabled for the repository due to the organization's settings. If "Secret scanning" is shown with an Enable button, you still need to enable secret scanning by clicking Enable. If you see a Disable button, secret scanning is already enabled.

Enabling additional features for secret scanning alerts for users
You can enable the following additional secret scanning features through your repository's "Code security and analysis" settings:
- Push protection. For more information, see "Push protection for repositories and organizations."
- Validity checks for partner patterns. For more infomation, see "Enabling validity checks for partner patterns."
- Scanning for non-provider patterns. For more information, see "Enabling scanning for non-provider patterns."
- AI-powered generic secret detection. For more information, see "Enabling AI-powered generic secret detection."
- Scanning for custom patterns. For more information, see "Defining custom patterns for secret scanning."
Enabling validity checks for partner patterns
Note: Validity checks for partner patterns is currently in beta and subject to change.
Validity checks for partner patterns is available on all types of repositories on GitHub.com. To use this feature, you must have a license for GitHub Advanced Security.
You can allow secret scanning to automatically check the validity of a secret found in your repository by sending it to the relevant partner. For more information on validity checks, see "Checking a secret's validity" in "Managing alerts from secret scanning."
Note: When you enable automatic validity checks for a repository, you also allow on-demand validity checks to be performed for patterns detected in that repository.
-
On GitHub.com, navigate to the main page of the repository.
-
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Code security and analysis.
-
Under Secret scanning, select the checkbox next to "Automatically verify if a secret is valid by sending it to the relevant partner".
You can also use the REST API to enable validity checks for partner patterns for your repository. For more information, see "REST API endpoints for repositories." Alternatively, organization owners and enterprise administrators can enable the feature for all repositories in the organization or enterprise settings. For more information, see "Managing security and analysis settings for your organization" and "Managing GitHub Advanced Security features for your enterprise."
Enabling scanning for non-provider patterns
Note: The detection of non-provider patterns is currently in beta and subject to change.
You can enable scanning for non-provider patterns. Non-provider patterns correspond to secrets such as private keys and they have a higher ratio of false positives.
-
On GitHub.com, navigate to the main page of the repository.
-
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Code security and analysis.
-
Under Secret scanning, select the checkbox next to "Scan for non-provider patterns".
For more information about non-provider patterns, see "Secret scanning patterns."
Enabling secret scanning alerts for users for all your user-owned public repositories
You can enable secret scanning for all of your existing user-owned public repositories through your personal account settings.
Note: As of March 11, 2024, secret scanning and push protection will be enabled by default for all new user-owned public repositories that you create. You can still choose to disable these features for an individual repository in the repository's "Code security and analysis" settings page. For more information, see "Managing security and analysis settings for your repository".
-
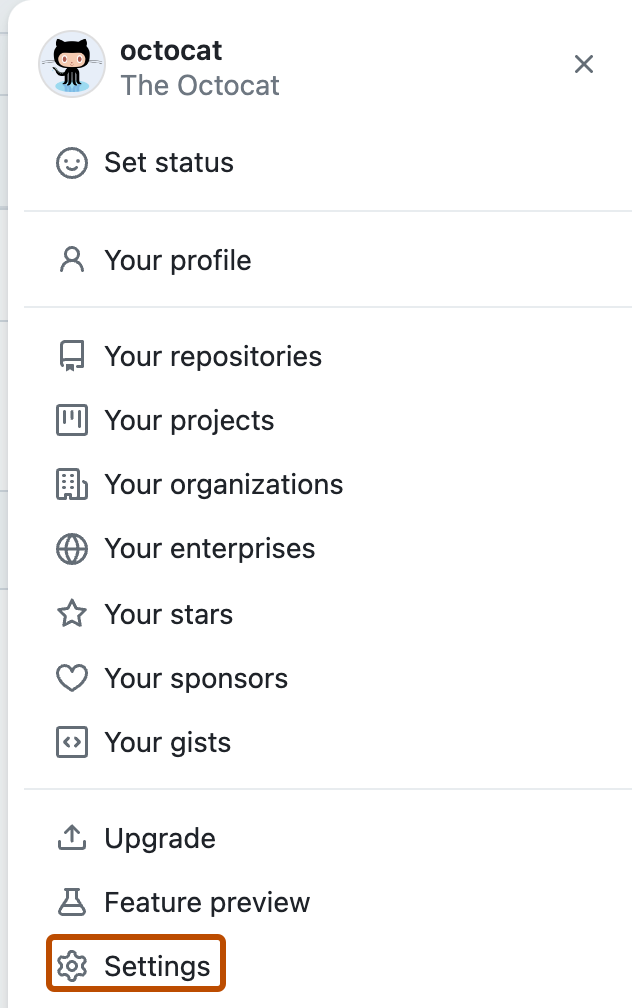
In the upper-right corner of any page, click your profile photo, then click Settings.
-
In the "Security" section of the sidebar, click Code security and analysis.
-
Under "Code security and analysis", to the right of "Secret scanning", click Disable all or Enable all.
-
Optionally, if you want to enable push protection, click Enable to the right of "Push protection." When you enable push protection for your organization or repository, secret scanning also checks pushes for supported secrets. Secret scanning lists any secrets it detects so the author can review the secrets and remove them or, if permitted, allow those secrets to be pushed. For more information, see "Push protection for repositories and organizations."

Excluding directories from secret scanning alerts for users
You can configure a secret_scanning.yml file to exclude directories from secret scanning, including when you use push protection. For example, you can exclude directories that contain tests or randomly generated content.
-
On GitHub.com, navigate to the main page of the repository.
-
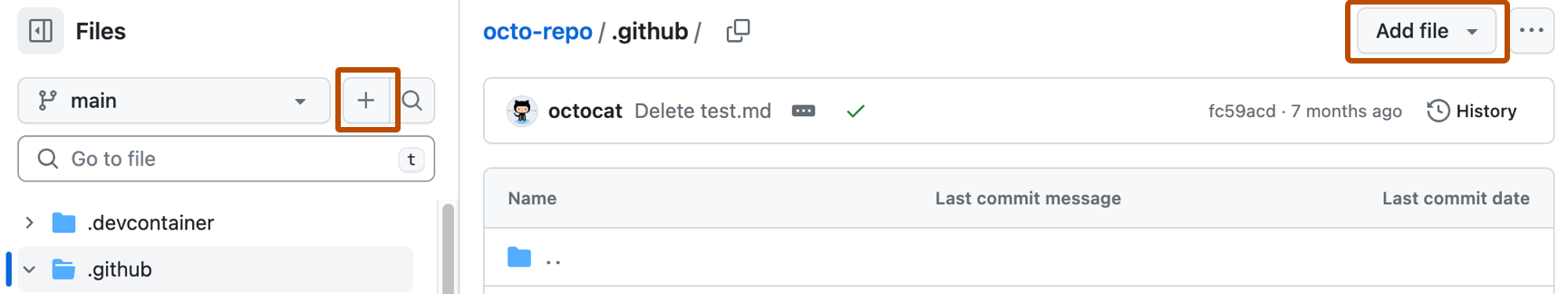
Above the list of files, select the Add file dropdown menu, then click Create new file.
Alternatively, you can click in the file tree view on the left.
-
In the file name field, type .github/secret_scanning.yml.
-
Under Edit new file, type
paths-ignore:followed by the paths you want to exclude from secret scanning.paths-ignore: - "foo/bar/*.js"You can use special characters, such as
*to filter paths. For more information about filter patterns, see "Workflow syntax for GitHub Actions."Notes:
- If there are more than 1,000 entries in
paths-ignore, secret scanning will only exclude the first 1,000 directories from scans. - If
secret_scanning.ymlis larger than 1 MB, secret scanning will ignore the entire file.
- If there are more than 1,000 entries in
You can also ignore individual alerts from secret scanning. For more information, see "Managing alerts from secret scanning."