비밀에 대한 정보
개발 환경 비밀은 조직, 리포지토리 또는 개인 계정용 GitHub Codespaces 설정에서 만든 암호화된 환경 변수입니다. 이 문서에서는 조직 비밀과 리포지토리 비밀을 관리하는 방법을 설명합니다. 구체적인 사용자 비밀을 만드는 방법에 대한 자세한 내용은 "GitHub Codespaces에 대한 계정별 비밀 관리" 을(를) 참조하세요.
개발 환경 비밀을 만들면 GitHub Codespaces에서 사용할 수 있습니다. GitHub은(는) libsodium 봉인인 상자를 사용하여 비밀을 GitHub에 도달하기 전에 암호화하고 codespace에서 사용할 때만 암호를 해독합니다.
조직 비밀을 사용하면 여러 리포지토리 간에 비밀을 공유할 수 있으므로 중복 비밀을 만들 필요가 줄어듭니다. 액세스 정책을 사용하여 조직 비밀을 사용할 수 있는 리포지토리를 제어할 수 있습니다.
비밀은 비밀을 만든 후 새 codespace를 만들거나 codespace를 다시 시작할 때 사용할 수 있습니다. GitHub.com에 비밀을 만들고 현재 실행 중인 codespace에서 비밀을 사용하려면 codespace를 중지한 다음 다시 시작합니다. codespace를 중지하는 방법에 대한 자세한 내용은 "Github Codespaces에서 Visual Studio Code 명령 팔레트 사용"을(를) 참조하세요.
비밀 이름 지정
비밀 이름에는 다음 규칙이 적용됩니다.
-
비밀 이름은 영숫자 문자(
[a-z],[A-Z],[0-9]) 또는 밑줄(_)만 포함할 수 있습니다. 공백은 사용할 수 없습니다. -
비밀 이름은
GITHUB_접두사로 시작해서는 안됩니다. -
비밀 이름은 숫자로 시작해서는 안됩니다.
-
비밀 이름은 대/소문자를 구분하지 않습니다.
-
비밀 이름은 만든 수준에서 고유해야 합니다. 예를 들어 리포지토리 수준에서 만든 비밀은 해당 리포지토리에 고유한 이름이 있어야 하고 조직 수준에서 만든 비밀에는 해당 수준에서 고유한 이름이 있어야 합니다.
이름이 같은 비밀이 여러 수준에 있는 경우 가장 낮은 수준의 비밀이 우선적으로 적용됩니다. 예를 들어 조직 수준 비밀의 이름이 리포지토리 수준 비밀과 동일한 경우 리포지토리 수준 비밀이 우선 적용됩니다.
비밀에 대한 제한
조직당 최대 100개의 비밀과 리포지토리당 100개의 비밀을 저장할 수 있습니다.
비밀의 크기는 48KB로 제한됩니다.
리포지토리에 권장되는 비밀
프로젝트에 특정 사용자 비밀이 필요할 수 있습니다. 예를 들어 codespace에서 응용 프로그램을 실행하려면 사용자가 개인 API 키를 제공해야 할 수 있습니다. 이 경우 개발 컨테이너 구성에서 권장되는 비밀을 지정할 수 있습니다. 그러면 고급 옵션 페이지를 사용하여 codespace를 만들 때 이러한 개인 비밀을 아직 만들지 않은 경우 이러한 비밀에 대한 값을 제공하라는 메시지가 사용자에게 표시됩니다. 사용자가 codespace에서 사용할 비밀 값을 제공하는 경우 이 비밀은 Codespaces에 대한 개인 설정에 추가됩니다. 나중에 이 리포지토리에 대한 codespace를 만들 때 이 비밀에 대한 값을 입력할 필요가 없습니다. 자세한 내용은 "리포지토리에 권장되는 비밀 지정"을(를) 참조하세요.
리포지토리에 대한 비밀 추가
조직 리포지토리에 대한 개발 환경 비밀을 만들려면 관리자 액세스 권한이 있어야 합니다.
-
GitHub.com에서 리포지토리의 기본 페이지로 이동합니다.
-
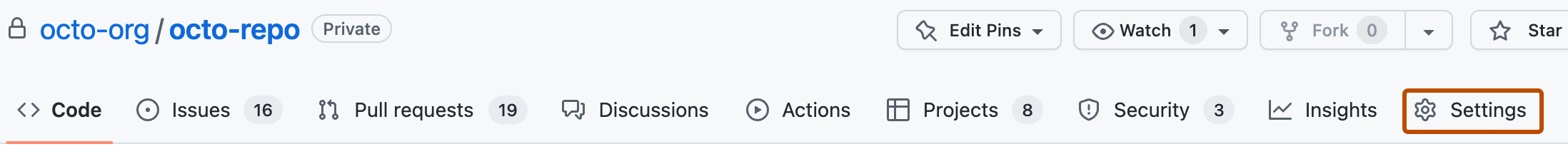
리포지토리 이름 아래에서 Settings(설정)를 클릭합니다. "설정" 탭이 표시되지 않으면 드롭다운 메뉴를 선택한 다음 설정을 클릭합니다.
-
사이드바의 "보안" 섹션에서 비밀 및 변수를 선택하고 Codespaces 을(를) 클릭합니다.
-
페이지 맨 위에서 새 리포지토리 비밀을 클릭합니다.
-
이름 입력 상자에 비밀의 이름을 입력합니다.
-
비밀 값을 입력합니다.
-
비밀 추가를 클릭합니다.
조직에 대한 비밀 추가
조직에서 개발 환경 비밀을 만들 때 정책을 사용하여 해당 비밀에 액세스할 수 있는 리포지토리를 제한할 수 있습니다. 예를 들어 모든 리포지토리에 대한 액세스 권한을 부여하거나 프라이빗 리포지토리 또는 지정된 리포지토리 목록에 대해서만 액세스를 제한할 수 있습니다.
조직 수준에서 비밀을 만들려면 admin 액세스 권한이 있어야 합니다.
-
GitHub.com에서 조직의 기본 페이지로 이동합니다.
-
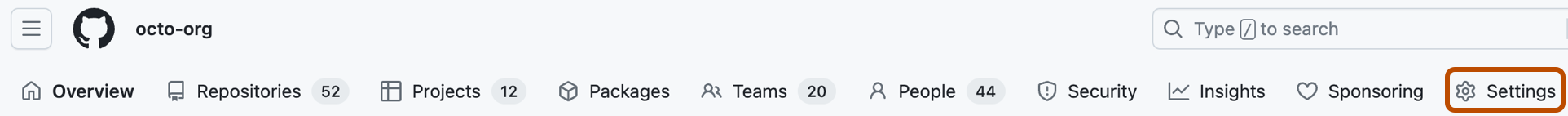
조직 이름에서 설정을 클릭합니다. "설정" 탭이 표시되지 않으면 드롭다운 메뉴를 선택한 다음 설정을 클릭합니다.
-
사이드바의 "보안" 섹션에서 비밀 및 변수를 선택하고 Codespaces 을(를) 클릭합니다.
-
페이지 맨 위에서 새 비밀을 클릭합니다.
-
이름 입력 상자에 비밀의 이름을 입력합니다.
-
값 필드에 비밀 값을 입력합니다.
-
리포지토리 액세스 드롭다운 목록에서 액세스 정책을 선택합니다.
-
비밀 추가를 클릭합니다.
조직 수준 비밀에 대한 액세스 검토
조직의 개발 환경 비밀에 적용되는 액세스 정책을 확인할 수 있습니다.
-
GitHub.com에서 조직의 기본 페이지로 이동합니다.
-
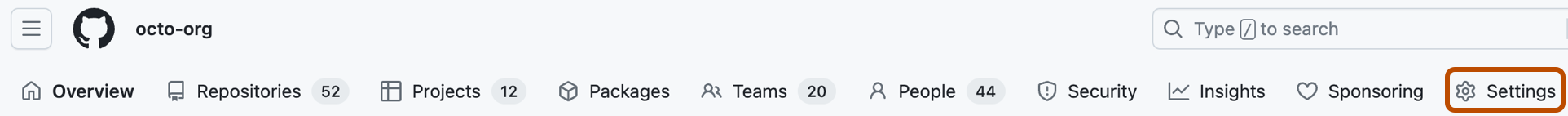
조직 이름에서 설정을 클릭합니다. "설정" 탭이 표시되지 않으면 드롭다운 메뉴를 선택한 다음 설정을 클릭합니다.
-
사이드바의 "보안" 섹션에서 비밀 및 변수를 선택하고 Codespaces 을(를) 클릭합니다.
-
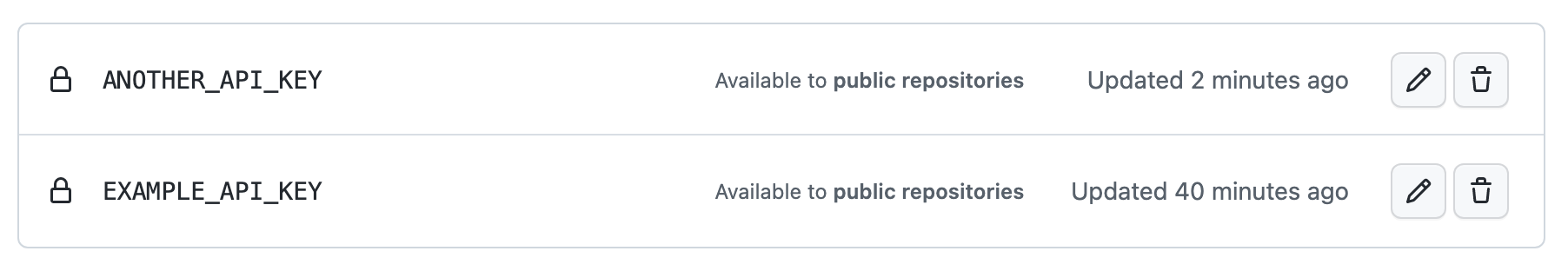
비밀 목록에는 구성된 사용 권한 및 정책이 포함됩니다. 예시:
-
각 비밀에 대해 구성된 권한에 대한 자세한 내용을 보려면 업데이트를 클릭하세요.