依存関係グラフの表示
Your site administrator must enable security alerts for vulnerable dependencies for your GitHub Enterprise Server instance before you can use this feature. For more information, see "Enabling alerts for vulnerable dependencies on GitHub Enterprise Server."
The dependency graph shows the dependencies of your repository. For information about the detection of dependencies and which ecosystems are supported, see "About the dependency graph."
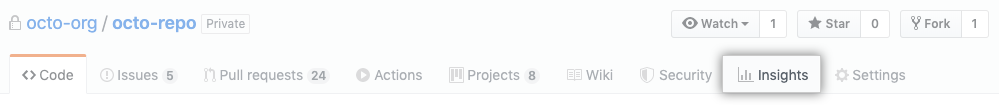
- GitHub Enterprise Serverで、リポジトリのメインページにアクセスしてください。
- リポジトリ名の下で Insights(インサイト)をクリックしてください。
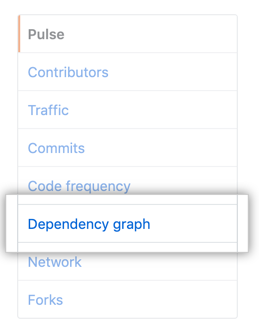
- 左のサイドバーでDependency graph(依存関係グラフ)をクリックしてください。
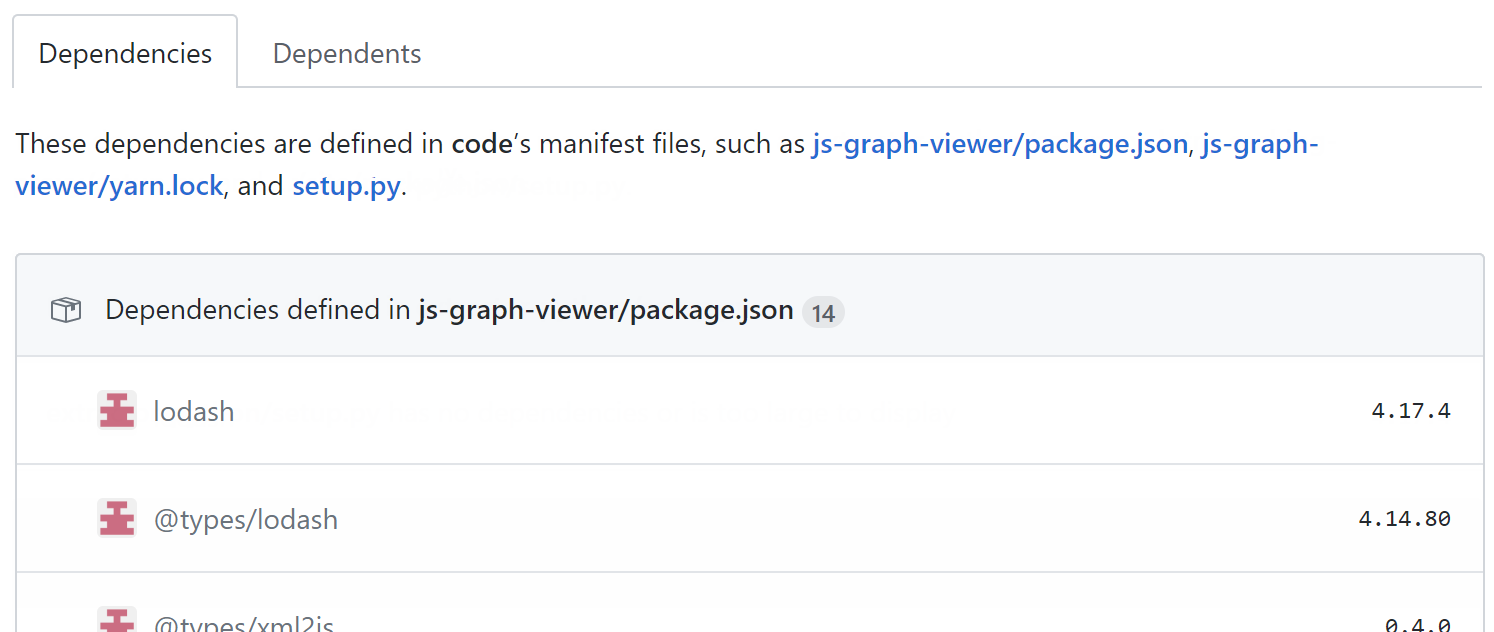
依存関係ビュー
Any direct and indirect dependencies that are specified in the repository's manifest or lock files are listed, grouped by ecosystem. If vulnerabilities have been detected in the repository, these are shown at the top of the view for users with access to security alerts.
Note: GitHub Enterprise Server does not populate the Dependents view.
Note: GitHub Enterprise Server does not populate the Dependents view.
依存関係グラフのトラブルシューティング
依存関係グラフが空の場合は、依存関係を含むファイルに問題があるかもしれません。 ファイルがファイルタイプに合わせて適切にフォーマットされているかをチェックしてください。
マニフェストまたはロックファイルが処理されない場合、その依存関係は依存関係グラフから省略され、脆弱な依存関係はチェックされなくなります。