Note: Your site administrator must enable code scanning for your GitHub Enterprise Server instance before you can use this feature. If you want to use GitHub Actions to scan your code, the site administrator must also enable GitHub Actions and set up the infrastructure required. For more information, see "Configuring code scanning for your appliance."
About code scanning
Code scanning helps you catch vulnerabilities in the code in your repository. With CodeQL code scanning, you can select custom or built-in query suites for use in your analysis, set a specific scan schedule, choose which events trigger a scan, and more.
Your site administrator can also make third-party actions available to users for code scanning, by setting up GitHub Connect. For more information, see "Configuring code scanning for your appliance."
If you run code scanning using multiple configurations, an alert will sometimes have multiple analysis origins. If an alert has multiple analysis origins, you can view the status of the alert for each analysis origin on the alert page. For more information, see "About code scanning alerts."
Note: This article describes the features available with the version of the CodeQL action and associated CodeQL CLI bundle included in the initial release of this version of GitHub Enterprise Server. If your enterprise uses a more recent version of the CodeQL action, see the GitHub Enterprise Cloud version of this article for information on the latest features. For information on using the latest version, see "Configuring code scanning for your appliance."
Prerequisites
Your repository is eligible for code scanning if it meets these requirements.
- It uses CodeQL-supported languages or you plan to generate code scanning results with a third-party tool.
- GitHub Actions are enabled.
- GitHub Advanced Security is enabled.
If the server on which you are running GitHub Enterprise Server is not connected to the internet, your site administrator can enable CodeQL code scanning by making the CodeQL analysis bundle available on the server. For more information, see "Configuring code scanning for your appliance."
Configuring code scanning using the CodeQL action
-
On your GitHub Enterprise Server instance, navigate to the main page of the repository.
-
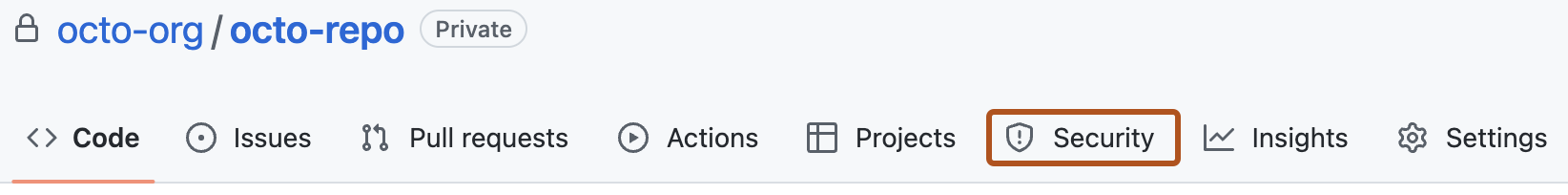
Under the repository name, click Security. If you cannot see the "Security" tab, select the dropdown menu, and then click Security.
-
To the right of "Code scanning alerts", click Set up code scanning. If "code scanning alerts" is missing, you need to ask an organization owner or repository administrator to enable GitHub Advanced Security. For more information, see "Managing security and analysis settings for your organization" or "Managing security and analysis settings for your repository."
-
Under "Get started with code scanning", click Set up this workflow on the CodeQL analysis workflow or on a third-party workflow.
Workflows are only displayed if they are relevant for the programming languages detected in the repository. The CodeQL analysis workflow is always displayed, but the "Set up this workflow" button is only enabled if CodeQL analysis supports the languages present in the repository.
-
To customize how code scanning scans your code, edit the workflow.
Generally, you can commit the CodeQL analysis workflow without making any changes to it. However, many of the third-party workflows require additional configuration, so read the comments in the workflow before committing.
For more information, see "Customizing code scanning" and "CodeQL code scanning for compiled languages."
-
Click Commit changes... to display the commit changes form.
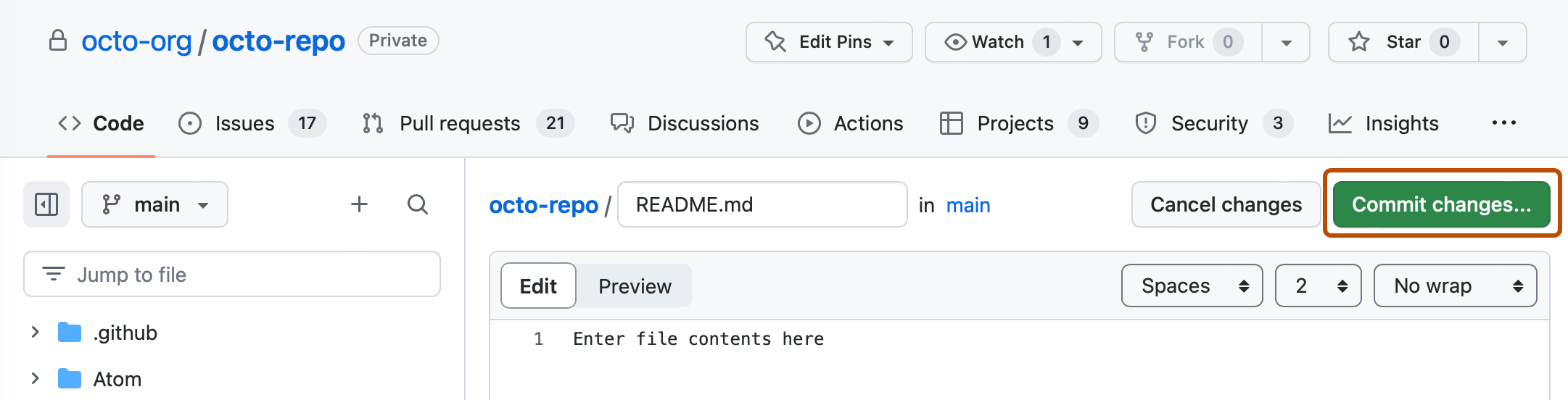
-
In the commit message field, type a commit message.
-
Choose whether you'd like to commit directly to the default branch, or create a new branch and start a pull request.
-
Click Commit new file or Propose new file.
In the suggested CodeQL analysis workflow, code scanning is configured to analyze your code each time you either push a change to the default branch or any protected branches, or raise a pull request against the default branch. As a result, code scanning will now commence.
The on:pull_request and on:push triggers for code scanning are each useful for different purposes. See "Customizing code scanning" and Triggering a workflow."
For information on bulk enablement, see "Configuring code scanning with CodeQL at scale."
Next steps
After your workflow runs successfully at least once, you are ready to start examining and resolving code scanning alerts. For more information on code scanning alerts, see "About code scanning alerts" and "Managing code scanning alerts for your repository."
Learn how code scanning runs behave as checks on pull requests, see "Triaging code scanning alerts in pull requests."