About Dependabot for GitHub Enterprise Server
Dependabot helps users of your GitHub Enterprise Server instance find and fix vulnerabilities in their dependencies.
With Dependabot alerts, GitHub identifies insecure dependencies in repositories and creates alerts on your GitHub Enterprise Server instance, using data from the GitHub Advisory Database and the dependency graph service.
We add advisories to the GitHub Advisory Database from the following sources:
- The National Vulnerability Database
- A combination of machine learning and human review to detect vulnerabilities in public commits on GitHub
- Security advisories reported on GitHub
- The npm Security advisories database
After you enable Dependabot alerts for your enterprise, vulnerability data is synced from the GitHub Advisory Database to your instance once every hour. Only GitHub-reviewed advisories are synchronized. For more information, see "Browsing security advisories in the GitHub Advisory Database."
You can also choose to manually sync vulnerability data at any time. For more information, see "Viewing the vulnerability data for your enterprise."
Note: When you enable Dependabot alerts, no code or information about code from your GitHub Enterprise Server instance is uploaded to GitHub.com.
When your GitHub Enterprise Server instance receives information about a vulnerability, it identifies repositories in your GitHub Enterprise Server instance that use the affected version of the dependency and generates Dependabot alerts. You can choose whether or not to notify users automatically about new Dependabot alerts.
For repositories with Dependabot alerts enabled, scanning is triggered on any push to the default branch that contains a manifest file or lock file. Additionally, when a new vulnerability record is added to your GitHub Enterprise Server instance, GitHub Enterprise Server scans all existing repositories on your GitHub Enterprise Server instance and generates alerts for any repository that is vulnerable. For more information, see "About Dependabot alerts."
Enabling Dependabot alerts
Before you can enable Dependabot alerts:
- You must enable GitHub Connect. For more information, see "Managing GitHub Connect."
- You must enable the dependency graph. For more information, see "Enabling the dependency graph for your enterprise."
-
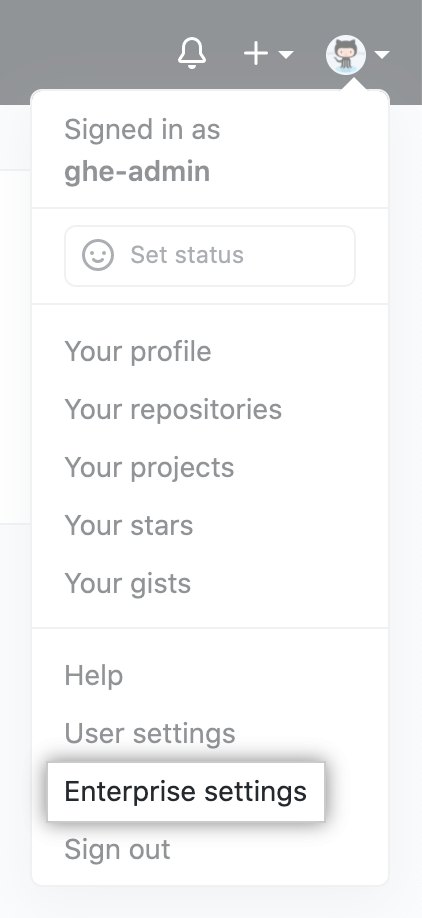
In the top-right corner of GitHub Enterprise Server, click your profile photo, then click Enterprise settings.
-
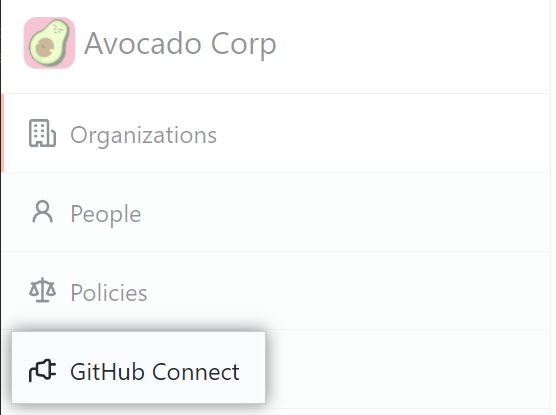
In the enterprise account sidebar, click GitHub Connect.
-
Under "Repositories can be scanned for vulnerabilities", select the drop-down menu and click Enabled without notifications. Optionally, to enable alerts with notifications, click Enabled with notifications.
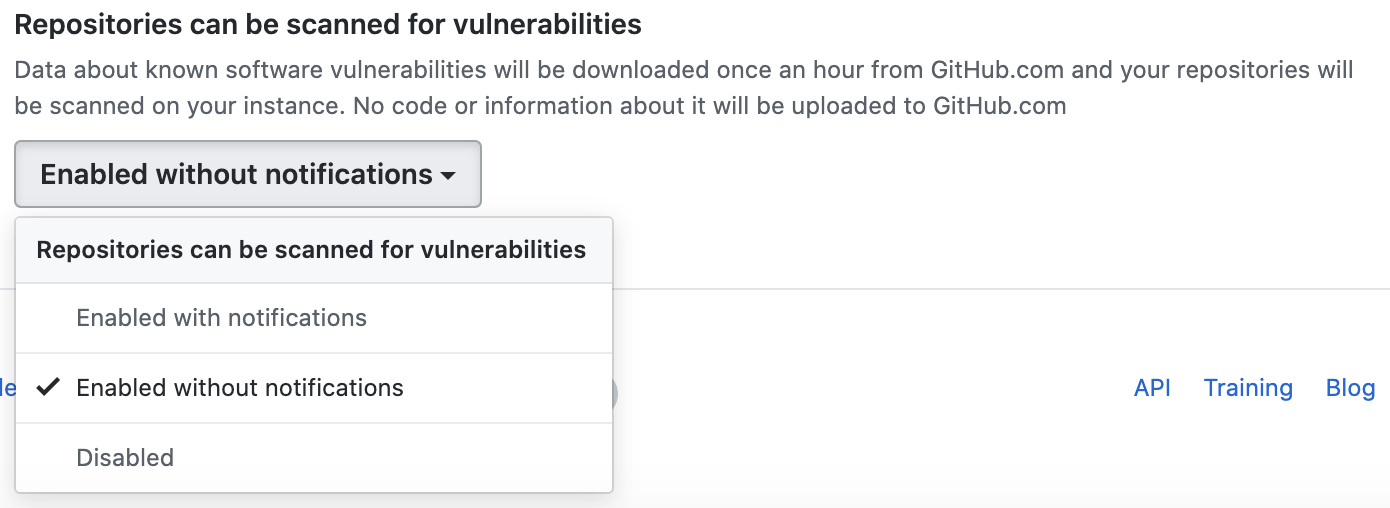
Tip: We recommend configuring Dependabot alerts without notifications for the first few days to avoid an overload of emails. After a few days, you can enable notifications to receive Dependabot alerts as usual.