关于 Enterprise Managed Users 的预配
若要在 GitHub.com 上为企业成员创建、管理和停用用户帐户,IdP 必须实施 SCIM,以便与 GitHub 通信。 SCIM 是一种管理不同系统间用户标识的开放规范。 不同的 IdP 提供不同的 SCIM 预配配置体验。
配置 Enterprise Managed Users 的预配后,你的 IdP 使用 SCIM 在 GitHub.com 上预配用户帐户并将这些帐户添加到企业。 如果将某个组分配给应用程序,你的 IdP 将为该组的所有成员预配新的 托管用户帐户。
如果使用合作伙伴 IdP,则可以使用合作伙伴 IdP 的应用程序简化 SCIM 预配的配置。 如果不使用合作伙伴 IdP 进行预配,则可以使用对 GitHub 的 REST API for SCIM 的调用来实现 SCIM,其为 beta 版,可能会更改。 有关详细信息,请参阅“关于 Enterprise Managed Users”。
SCIM 管理企业中用户帐户的生命周期。 在 IdP 上更新与用户标识关联的信息时,IdP 将在 GitHub.com 上更新用户的帐户。 从 Enterprise Managed Users 的 IdP 应用程序取消分配用户或停用 IdP 上的用户帐户时,IdP 将与 GitHub 进行通信,以使任何会话失效并禁用该成员的帐户。 已禁用帐户的信息会保留,其用户名将更改为原始用户名的哈希,并追加短代码。 如果将用户重新分配给 Enterprise Managed Users 的 IdP 应用程序或在 IdP 上重新激活其帐户,则会重新激活 GitHub 上的 托管用户帐户,并将还原用户名。
要配置团队和组织成员身份、存储库访问权限以及 GitHub Enterprise Cloud 上的权限,可以使用 IdP 上的组。 有关详细信息,请参阅“使用标识提供者组管理团队成员身份”。
先决条件
- 在完成预配之前,必须为你的用户配置身份验证。 此配置要求在身份管理系统和 GitHub Enterprise Cloud 上进行设置。 有关详细信息,请参阅“为企业托管用户配置身份验证”。
- 在配置预配之前,请确保了解对 IdP 的集成要求和支持级别。 有关详细信息,请参阅“关于 Enterprise Managed Users”。
创建 personal access token
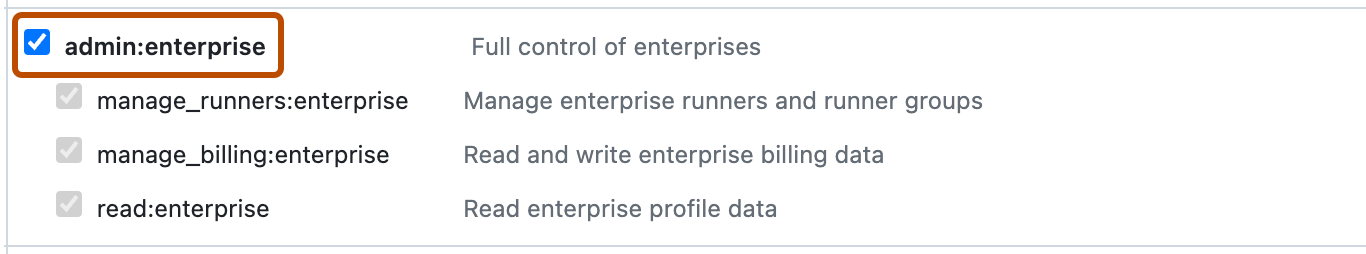
若要为 具有托管用户的企业 配置预配,需要使用属于安装用户的作用域为 admin:enterprise 的 personal access token (classic)。
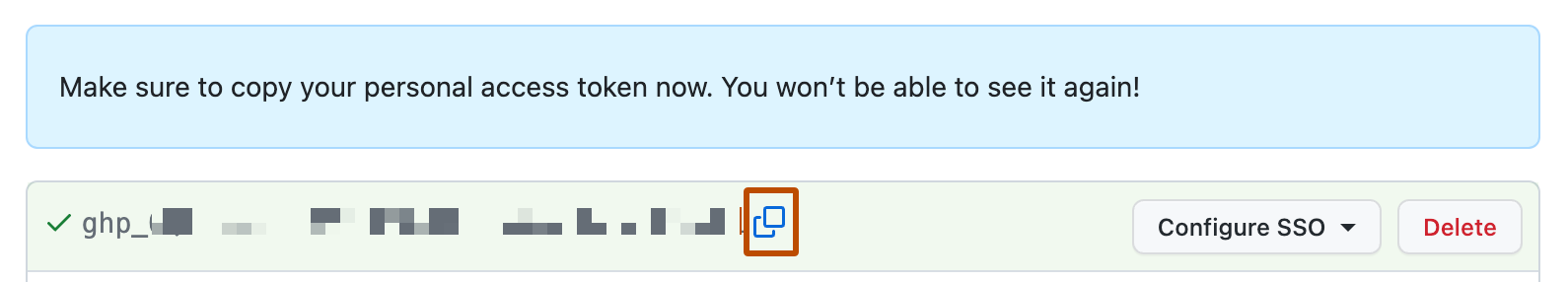
警告: 如果令牌过期或预配的用户创建了令牌,SCIM 预配可能会意外停止工作。 请确保在以安装用户身份登录时创建令牌,并将令牌过期设置为“不过期”。
-
使用用户名“@SHORT-CODE_admin”以新企业的安装用户身份登录到 GitHub.com。
-
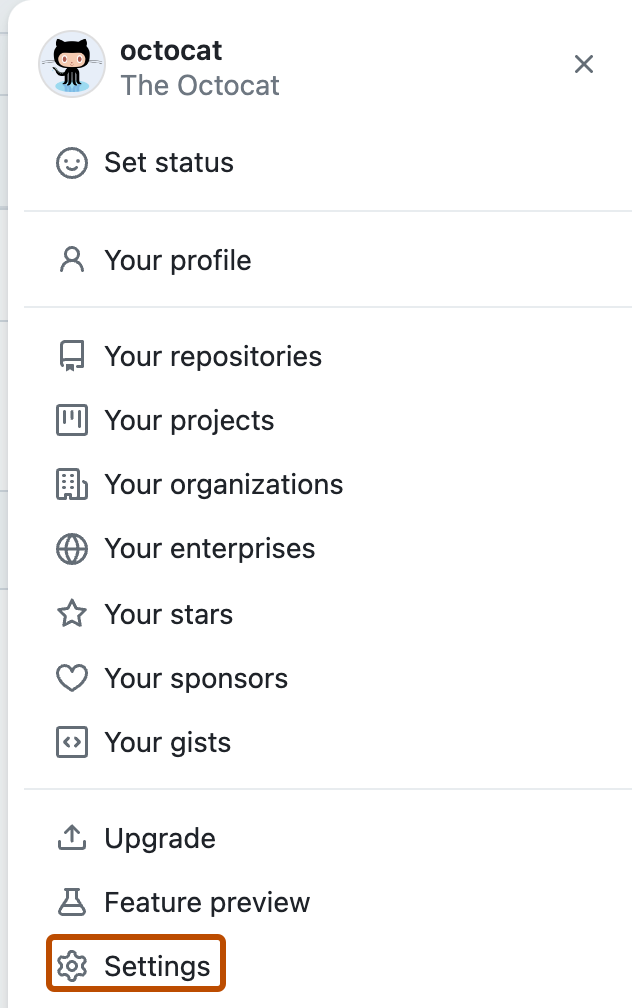
在任何页面的右上角,单击个人资料照片,然后单击“设置”。
-
在左侧边栏中,单击“ 开发人员设置”。
-
在左侧边栏中,单击“Personal access token”。
-
单击“生成新令牌”。
-
在“备注”下,为令牌提供描述性名称。
-
选择“过期”下拉菜单,然后单击“不过期” 。
-
选择 admin:enterprise 作用域。
-
单击“生成令牌”。****
-
要将令牌复制到剪贴板,请单击 。
-
若要保存令牌以供以后使用,请将新令牌安全地存储在密码管理器中。
为 Enterprise Managed Users 配置预配
创建 personal access token 并将其安全地存储后,可以在 IdP 上配置预配。 你应该遵循的说明各不相同,具体取决于你是否使用合作伙伴 IdP 的应用程序来进行身份验证和预配。
如果使用合作伙伴 IdP 的应用程序,请配置预配
要使用合作伙伴 IdP 的应用程序进行身份验证和预配,请查看下表链接中合作伙伴的配置预配说明。
| IdP | SSO 方法 | 详细信息 |
|---|---|---|
| Microsoft Entra ID(以前称为 Azure AD) | OIDC | Microsoft Learn 上的教程:为 GitHub Enterprise Managed User (OIDC) 配置自动用户预配 |
| Entra ID | SAML | Microsoft Learn 上的教程:为 GitHub Enterprise Managed User 配置自动用户预配 |
| Okta | SAML | "使用 Okta 配置 SCIM 预配" |
| PingFederate | SAML | PingFederate 文档中的配置 PingFederate 以实现预配和 SSO 和管理通道 |
或者,如果在合作伙伴 IdP 上配置了身份验证,但你想要从其他身份管理系统预配用户,则可以让 IdP 调用 GitHub 的 REST API 终结点,以进行 SCIM 预配。
为其他身份管理系统配置预配
如果不使用合作伙伴 IdP,或者仅使用合作伙伴 IdP 进行身份验证,则可使用 GitHub 的 REST API 终结点来管理用户帐户的生命周期,以便进行 SCIM 预配。 这些终结点目前为公共 beta 版本,可能会有变动。 有关详细信息,请参阅“使用 REST API 通过 SCIM 预配用户和组”。
-
使用用户名 @SHORT-CODE_admin 以企业的设置用户身份登录到 GitHub.com,其中 SHORT-CODE 需替换为企业的短代码。
注意****:如果需要重置设置用户的密码,请通过 GitHub 支持门户 联系 GitHub 支持。
-
在 GitHub.com 的右上角,单击你的个人资料照片,然后单击“你的企业”。
-
在企业列表中,单击您想要查看的企业。
-
在企业帐户边栏中,单击“设置”。
-
在“ 设置”下,单击“身份验证安全性” 。
-
在“打开 SCIM 配置”下,选择“启用开放式 SCIM 配置”。
-
通过调用 REST API 终结点进行 SCIM 预配,从而管理用户的生命周期。 有关详细信息,请参阅“使用 REST API 通过 SCIM 预配用户和组”。
分配用户和组
配置身份验证和预配后,可以通过将用户或组分配到 GitHub Enterprise Managed User 应用程序在 GitHub.com 上预配新用户。
分配用户时,可以使用 GitHub Enterprise Managed User 应用程序中的“角色”属性在 GitHub Enterprise Cloud 上设置用户在企业中的角色。 有关可分配的角色的详细信息,请参阅“企业中的角色”。
Entra ID 不支持预配嵌套组。 有关详细信息,请参阅 Microsoft Learn 中的应用程序预配在 Microsoft Entra ID 中是如何工作的。