Accessing the audit log
The audit log lists actions performed within the last 90 days. Only owners can access an organization's audit log.
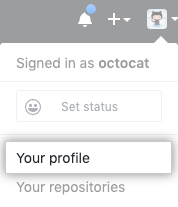
- En la esquina superior derecha de GitHub Enterprise, da clic en tu foto de perfil, posteriormente, da clic en Tu perfil.
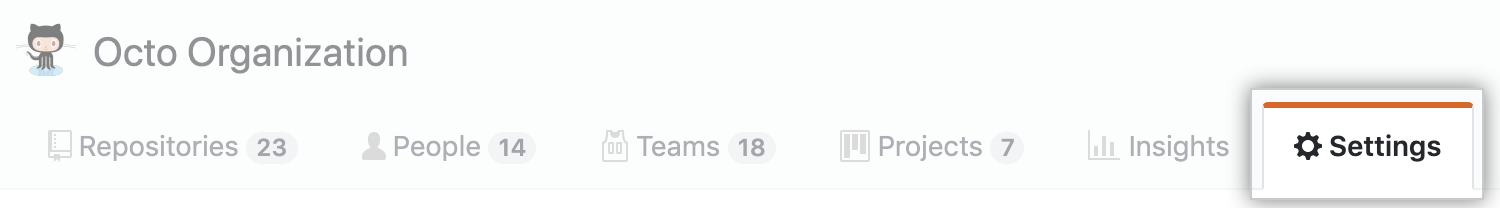
- En la parte izquierda de tu página de perfil, debajo de "Organizaciones", da clic en el icono de tu organización.

- Debajo de tu nombre de organización, da clic en Configuración.
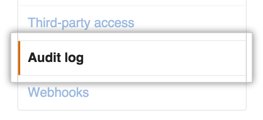
- En la barra lateral de Parámetros, haz clic en Audit Log (Registro de auditoría).
Searching the audit log
El registro lista la siguiente información sobre cada acción:
- En qué repositorio se realizó una acción
- El usuario que realizó la acción
- La acción que se realizó
- En qué país se realizó la acción
- La fecha y hora en que se produjo la acción
Nota que no puedes buscar entradas utilizando texto. Sin embargo, puedes construir consultas de búsqueda utilizando una variedad de filtros. Muchos operadores que se utilizan cuando se busca el registro por queries, tales como -, >, o <, empatan con el mismo formato que si se busca con GitHub Enterprise. Para obtener más información, consulta la sección "Buscar en GitHub".
Búsqueda basada en la operación
Utiliza el calificador operation para limitar las acciones en tipos específicos de operaciones. Por ejemplo:
operation:accessencuentra todos los eventos en donde se accedió a un recurso.operation:authenticationencuentra todos los eventos en donde se realizó un evento de autenticación.operation:createencuentra todos los eventos en donde se creó un recurso.operation:modifyencuentra todos los eventos en donde se modificó un recurso existente.operation:removeencuentra todos los eventos en donde se eliminó un recurso existente.operation:restoreencuentra todos los eventos en donde se restauró un recurso existente.operation:transferencuentra todos los eventos en donde se transfirió un recurso existente.
Búsqueda basada en el repositorio
Utiliza el calificador repo para limitar las acciones a un repositorio específico. Por ejemplo:
repo:my-org/our-repoencuentra todos los eventos que ocurrieron para el repositorioour-repoen la organizaciónmy-org.repo:my-org/our-repo repo:my-org/another-repoencuentra todos los eventos que ocurrieron tanto para los repositoriosour-repocomoanother-repoen la organizaciónmy-org.-repo:my-org/not-this-repoexcluye todos los eventos que ocurrieron para el repositorionot-this-repoen la organizaciónmy-org.
Nota que debes incluir el nombre de cuenta dentro del calificador repo; no funcionará si buscas únicamente repo:our-repo.
Búsqueda basada en el usuario
El calificador actor puede incluir eventos que se basen en quién realizó la acción. Por ejemplo:
actor:octocatencuentra todos los eventos realizados poroctocat.actor:octocat actor:hubotencuentra todos los eventos realizados tanto poroctocatcomo porhubot.-actor:hubotexcluye todos los eventos realizados porhubot.
Ten en cuenta que solo puedes utilizar un nombre de usuario GitHub Enterprise, no el nombre real de una persona.
Search based on the action performed
To search for specific events, use the action qualifier in your query. Actions listed in the audit log are grouped within the following categories:
| Category Name | Description |
|---|---|
discussion_post | Contains all activities related to discussions posted to a team page. |
discussion_post_reply | Contains all activities related to replies to discussions posted to a team page. |
hook | Contains all activities related to webhooks. |
integration_installation_request | Contains all activities related to organization member requests for owners to approve integrations for use in the organization. |
org | Contains all activities related to organization membership |
profile_picture | Contains all activities related to your organization's profile picture. |
project | Contains all activities related to project boards. |
protected_branch | Contains all activities related to protected branches. |
repo | Contains all activities related to the repositories owned by your organization. |
repository_vulnerability_alert | Contains all activities related to security alerts for vulnerable dependencies. |
team | Contains all activities related to teams in your organization. |
team_discussions | Contains activities related to managing team discussions for an organization. |
You can search for specific sets of actions using these terms. For example:
action:teamfinds all events grouped within the team category.-action:hookexcludes all events in the webhook category.
Each category has a set of associated events that you can filter on. For example:
action:team.createfinds all events where a team was created.-action:hook.events_changedexcludes all events where the events on a webhook have been altered.
This list describes the available categories and associated events:
- The
discussion_postcategory - The
discussion_post_replycategory - The
hookcategory - The
integration_installation_requestcategory - The
issuecategory - The
orgcategory - The
oauth_applicationcategory - The
profile_picturecategory - The
projectcategory - The
protected_branchcategory - The
repocategory - The
repository_vulnerability_alertcategory - The
teamcategory - The
team_discussionscategory
The discussion_post category
| Action | Description |
|---|---|
update | Triggered when a team discussion post is edited. |
destroy | Triggered when a team discussion post is deleted. |
The discussion_post_reply category
| Action | Description |
|---|---|
update | Triggered when a reply to a team discussion post is edited. |
destroy | Triggered when a reply to a team discussion post is deleted. |
The hook category
| Action | Description |
|---|---|
create | Triggered when a new hook was added to a repository owned by your organization. |
config_changed | Triggered when an existing hook has its configuration altered. |
destroy | Triggered when an existing hook was removed from a repository. |
events_changed | Triggered when the events on a hook have been altered. |
The integration_installation_request category
| Action | Description |
|---|---|
create | Triggered when an organization member requests that an organization owner install an integration for use in the organization. |
close | Triggered when a request to install an integration for use in an organization is either approved or denied by an organization owner, or canceled by the organization member who opened the request. |
The issue category
| Action | Description |
|---|---|
destroy | Triggered when an organization owner or someone with admin permissions in a repository deletes an issue from an organization-owned repository. |
The org category
| Action | Description |
|---|---|
disable_member_team_creation_permission | Triggered when an organization owner limits team creation to owners. For more information, see "Setting team creation permissions in your organization." |
disable_two_factor_requirement | Triggered when an owner disables a two-factor authentication requirement for all members and outside collaborators in an organization. |
enable_member_team_creation_permission | Triggered when an organization owner allows members to create teams. For more information, see "Setting team creation permissions in your organization." |
enable_two_factor_requirement | Triggered when an owner requires two-factor authentication for all members and outside collaborators in an organization. |
invite_member | Triggered when a new user was invited to join your organization. |
remove_member | Triggered when an owner removes a member from an organization or when two-factor authentication is required in an organization and an organization member doesn't use 2FA or disables 2FA. Also triggered when an organization member removes themselves from an organization. |
remove_outside_collaborator | Triggered when an owner removes an outside collaborator from an organization or when two-factor authentication is required in an organization and an outside collaborator does not use 2FA or disables 2FA. |
update_default_repository_permission | Triggered when an owner changes the default repository permission level for organization members. |
update_member | Triggered when an owner changes a person's role from owner to member or member to owner. |
update_member_repository_creation_permission | Triggered when an owner changes the create repository permission for organization members. |
The oauth_application category
| Action | Description |
|---|---|
create | Triggered when a new App OAuth is created. |
destroy | Triggered when an existing App OAuth is deleted. |
reset_secret | Triggered when an App OAuth's client secret is reset. |
revoke_tokens | Triggered when an App OAuth's user tokens are revoked. |
transfer | Triggered when an existing App OAuth is transferred to a new organization. |
The profile_picture category
| Action | Description |
|---|---|
| update | Triggered when you set or update your organization's profile picture. |
The project category
| Action | Description |
|---|---|
create | Triggered when a project board is created. |
link | Triggered when a repository is linked to a project board. |
rename | Triggered when a project board is renamed. |
update | Triggered when a project board is updated. |
delete | Triggered when a project board is deleted. |
unlink | Triggered when a repository is unlinked from a project board. |
update_org_permission | Triggered when the base-level permission for all organization members is changed or removed. |
update_team_permission | Triggered when a team's project board permission level is changed or when a team is added or removed from a project board. |
update_user_permission | Triggered when an organization member or outside collaborator is added to or removed from a project board or has their permission level changed. |
The protected_branch category
| Action | Description |
|---|---|
create | Triggered when branch protection is enabled on a branch. |
destroy | Triggered when branch protection is disabled on a branch. |
update_admin_enforced | Triggered when branch protection is enforced for repository administrators. |
update_require_code_owner_review | Triggered when enforcement of required Code Owner review is updated on a branch. |
dismiss_stale_reviews | Triggered when enforcement of dismissing stale pull requests is updated on a branch. |
update_signature_requirement_enforcement_level | Triggered when enforcement of required commit signing is updated on a branch. |
update_pull_request_reviews_enforcement_level | Triggered when enforcement of required pull request reviews is updated on a branch. |
update_required_status_checks_enforcement_level | Triggered when enforcement of required status checks is updated on a branch. |
update_strict_required_status_checks_policy | Triggered when the requirement for a branch to be up to date before merging is changed. |
rejected_ref_update | Triggered when a branch update attempt is rejected. |
policy_override | Triggered when a branch protection requirement is overridden by a repository administrator. |
The repo category
| Action | Description |
|---|---|
access | Triggered when a repository owned by an organization is switched from "private" to "public" (or vice versa). |
add_member | Triggered when a user accepts an invitation to have collaboration access to a repository. |
add_topic | Triggered when a repository admin adds a topic to a repository. |
archived | Triggered when a repository admin archives a repository. |
config.disable_anonymous_git_access | Triggered when anonymous Git read access is disabled in a public repository. |
config.enable_anonymous_git_access | Triggered when anonymous Git read access is enabled in a public repository. |
config.lock_anonymous_git_access | Triggered when a repository's anonymous Git read access setting is locked. |
config.unlock_anonymous_git_access | Triggered when a repository's anonymous Git read access setting is unlocked. |
create | Triggered when a new repository is created. |
destroy | Triggered when a repository is deleted. |
enable | Triggered when a repository is reenabled. |
remove_member | Triggered when a user is removed from a repository as a collaborator. |
remove_topic | Triggered when a repository admin removes a topic from a repository. |
rename | Triggered when a repository is renamed. |
transfer | Triggered when a repository is transferred. |
transfer_start | Triggered when a repository transfer is about to occur. |
unarchived | Triggered when a repository admin unarchives a repository. |
The repository_vulnerability_alert category
| Action | Description |
|---|---|
create | Triggered when GitHub Enterprise creates a security alert for a vulnerable dependency in a particular repository. |
resolve | Triggered when someone with write access to a repository pushes changes to update and resolve a vulnerability in a project dependency. |
dismiss | Triggered when an organization owner or person with admin access to the repository dismisses a security alert about a vulnerable dependency. |
The team category
| Action | Description |
|---|---|
add_member | Triggered when a member of an organization is added to a team. |
add_repository | Triggered when a team is given control of a repository. |
change_parent_team | Triggered when a child team is created or a child team's parent is changed. |
change_privacy | Triggered when a team's privacy level is changed. |
create | Triggered when a new team is created. |
destroy | Triggered when a team is deleted from the organization. |
remove_member | Triggered when a member of an organization is removed from a team. |
remove_repository | Triggered when a repository is no longer under a team's control. |
The team_discussions category
| Action | Description |
|---|---|
disable | Triggered when an organization owner disables team discussions for an organization. For more information, see "Disabling team discussions for your organization." |
enable | Triggered when an organization owner enables team discussions for an organization. |
Search based on time of action
Use the created qualifier to filter actions in the audit log based on when they occurred. El formato de fecha debe seguir el estándar ISO8601, el cual es YYYY-MM-DD (año-mes-día). También puedes agregar información de tiempo ocpional THH:MM:SS+00:00 después de la fecha, para buscar por hora, minuto y segundo. Se hace agregando T, seguido de HH:MM:SS (hora-minutos-segundos), y un intervalo de UTC (+00:00).
Las fechas son compatibles con calificadores de mayor qué, menor qué y rango. For example:
created:2014-07-08finds all events that occurred on July 8th, 2014.created:>=2014-07-08finds all events that occurred on or after July 8th, 2014.created:<=2014-07-08finds all events that occurred on or before July 8th, 2014.created:2014-07-01..2014-07-31finds all events that occurred in the month of July 2014.
The audit log contains data for the past 90 days, but you can use the created qualifier to search for events earlier than that.
Search based on location
Using the qualifier country, you can filter actions in the audit log based on the originating country. You can use a country's two-letter short code or its full name. Keep in mind that countries with spaces in their name will need to be wrapped in quotation marks. For example:
country:definds all events that occurred in Germany.country:Mexicofinds all events that occurred in Mexico.country:"United States"all finds events that occurred in the United States.
Using the Audit log API
Note: The Audit log API is available for organizations using GitHub Enterprise.
To ensure a secure IP and maintain compliance for your organization, you can use the Audit log API to keep copies of your audit log data and monitor:
- Access to your organization or repository settings.
- Changes in permissions.
- Added or removed users in an organization, repository, or team.
- Users being promoted to admin.
- Changes to permissions of a GitHub App.
The GraphQL response can include data for up to 90 to 120 days.
For example, you can make a GraphQL request to see all the new organization members added to your organization. For more information, see the "GraphQL API Audit Log."