About provisioning for Enterprise Managed Users
To create, manage, and deactivate user accounts for your enterprise members on GitHub.com, your IdP must implement SCIM for communication with GitHub. SCIM is an open specification for management of user identities between systems. Different IdPs provide different experiences for the configuration of SCIM provisioning.
After you configure provisioning for Enterprise Managed Users, your IdP uses SCIM to provision user accounts on GitHub.com and add the accounts to your enterprise. If you assign a group to the application, your IdP will provision new managed user accounts for all members of the group.
If you use a partner IdP, you can simplify the configuration of SCIM provisioning by using the partner IdP's application. If you don't use a partner IdP for provisioning, you can implement SCIM using calls to GitHub's REST API for SCIM, which is in beta and subject to change. For more information, see "About Enterprise Managed Users."
SCIM manages the lifecycle of user accounts in your enterprise. When you update information associated with a user's identity on your IdP, your IdP will update the user's account on GitHub. When you unassign the user from the IdP application for Enterprise Managed Users or deactivate a user's account on your IdP, your IdP will communicate with GitHub to invalidate any sessions and disable the member's account. The disabled account's information is maintained and their username is changed to a hash of their original username with the short code appended. If you reassign a user to the IdP application for Enterprise Managed Users or reactivate their account on your IdP, the managed user account on GitHub will be reactivated, and the username will be restored.
To configure team and organization membership, repository access, and permissions on GitHub Enterprise Cloud, you can use groups on your IdP. For more information, see "Managing team memberships with identity provider groups."
Prerequisites
- Before you configure provisioning, you must configure authentication for your users. This configuration requires setup on both your identity management system and GitHub Enterprise Cloud. For more information, see "Configuring authentication for Enterprise Managed Users."
- Before you configure provisioning, ensure that you understand the integration requirements and level of support for your IdP. For more information, see "About Enterprise Managed Users."
Creating a personal access token
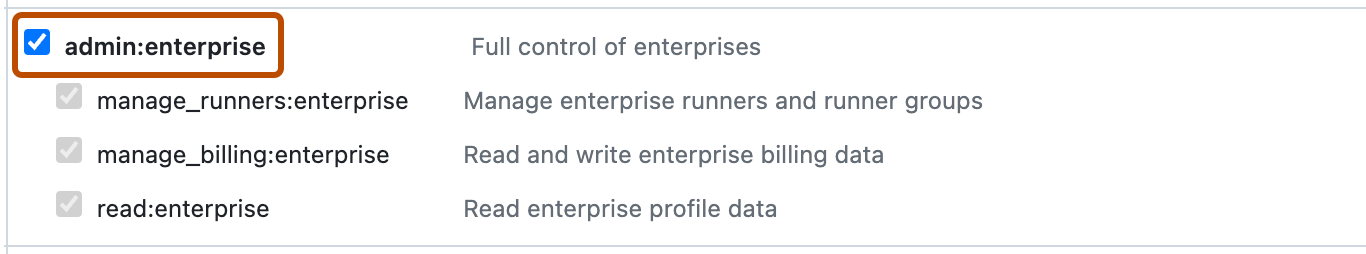
To configure provisioning for your enterprise with managed users, you need a personal access token (classic) with the admin:enterprise scope that belongs to the setup user.
Warning: If the token expires or a provisioned user creates the token, SCIM provisioning may unexpectedly stop working. Make sure that you create the token while signed in as the setup user and that the token expiration is set to "No expiration".
-
Sign into GitHub as the setup user for your new enterprise with the username @SHORT-CODE_admin.
-
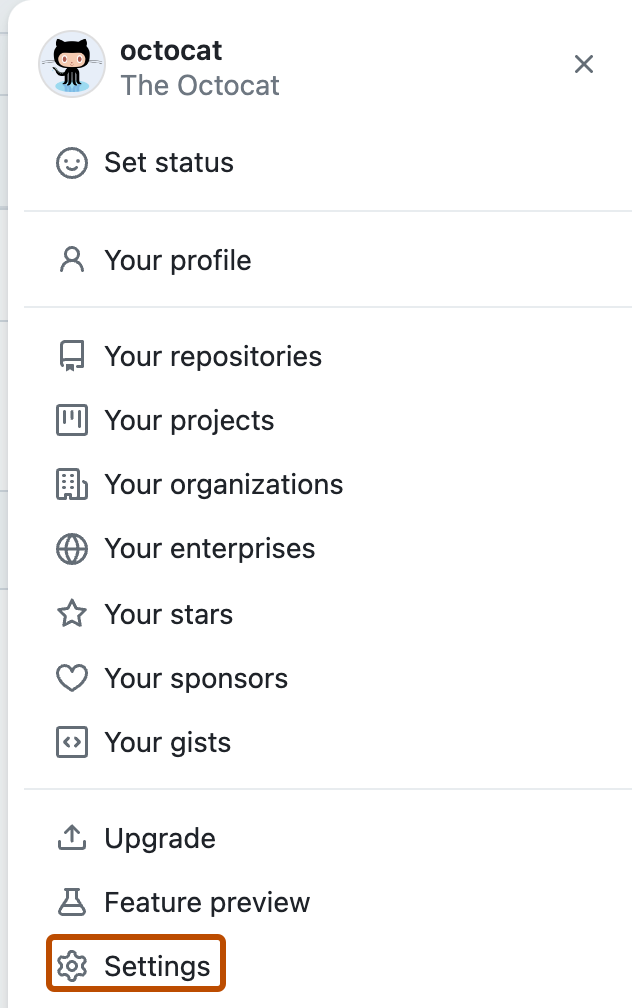
In the upper-right corner of any page, click your profile photo, then click Settings.
-
In the left sidebar, click Developer settings.
-
In the left sidebar, click Personal access tokens.
-
Click Generate new token.
-
Under Note, give your token a descriptive name.
-
Select the Expiration dropdown menu, then click No expiration.
-
Select the admin:enterprise scope.
-
Click Generate token.
-
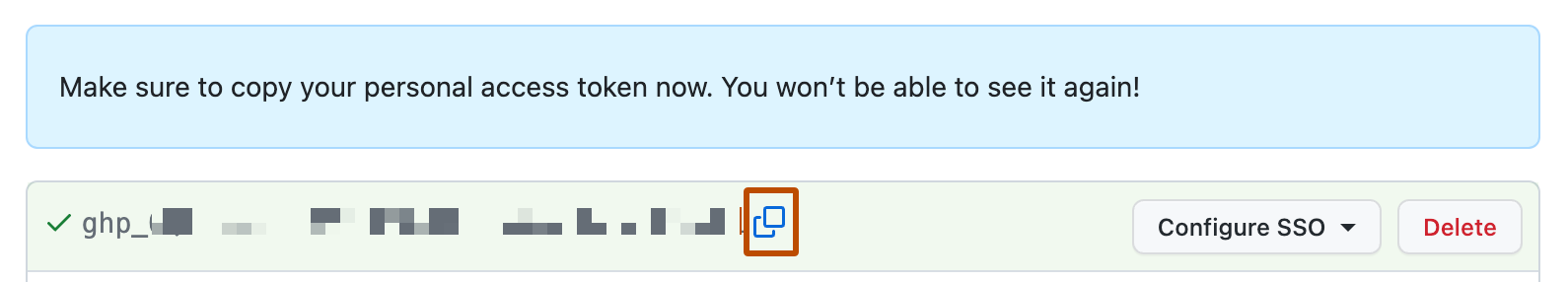
To copy the token to your clipboard, click .
-
To save the token for use later, store the new token securely in a password manager.
Configuring provisioning for Enterprise Managed Users
After creating your personal access token and storing it securely, you can configure provisioning on your IdP. The instructions you should follow differ depending on whether you use a partner IdP's application for both authentication and provisioning.
- Configuring provisioning if you use a partner IdP's application
- Configuring provisioning for other identity management systems
Configuring provisioning if you use a partner IdP's application
To use a partner IdP's application both authentication and provisioning, review the partner's instructions for configuring provisioning in the links in the following table.
| IdP | SSO method | More information |
|---|---|---|
| Microsoft Entra ID (previously known as Azure AD) | OIDC | Tutorial: Configure GitHub Enterprise Managed User (OIDC) for automatic user provisioning on Microsoft Learn |
| Entra ID | SAML | Tutorial: Configure GitHub Enterprise Managed User for automatic user provisioning on Microsoft Learn |
| Okta | SAML | "Configuring SCIM provisioning with Okta" |
| PingFederate | SAML | Configure PingFederate for provisioning and SSO and Managing channels in the PingFederate documentation |
Alternatively, if you configured authentication on a partner IdP, but you would like to provision users from a different identity management system, you can have your IdP make calls to GitHub's REST API endpoints for SCIM provisioning.
Configuring provisioning for other identity management systems
If you don't use a partner IdP, or if you only use a partner IdP for authentication, you can manage the lifecycle of user accounts using GitHub's REST API endpoints for SCIM provisioning. These endpoints are in beta and subject to change. For more information, see "Provisioning users and groups with SCIM using the REST API."
-
Sign into GitHub.com as the setup user for your enterprise with the username SHORT-CODE_admin, replacing SHORT-CODE with your enterprise's short code.
Note: If you need to reset the password for your setup user, contact GitHub Support through the GitHub Support portal.
-
In the top-right corner of GitHub.com, click your profile photo, then click Your enterprises.
-
In the list of enterprises, click the enterprise you want to view.
-
In the enterprise account sidebar, click Settings.
-
Under Settings, click Authentication security.
-
Under "Open SCIM Configuration", select "Enable open SCIM configuration".
-
Manage the lifecycle of your users by making calls to the REST API endpoints for SCIM provisioning. For more information, see "Provisioning users and groups with SCIM using the REST API."
Assigning users and groups
After you have configured authentication and provisioning, you will be able to provision new users on GitHub.com by assigning users or groups to the GitHub Enterprise Managed User application.
When assigning users, you can use the "Roles" attribute in the GitHub Enterprise Managed User application to set a user's role in your enterprise on GitHub Enterprise Cloud. For more information about the roles available to assign, see "Roles in an enterprise."
Entra ID does not support provisioning nested groups. For more information, see How Application Provisioning works in Microsoft Entra ID on Microsoft Learn.